When a security incident happens, chaos often follows. Teams scramble to verify facts, executives demand answers, and stakeholders need reassurance. Without a clear communication plan, this can lead to confusion, delays, and reputational damage. Here’s the solution: a structured communication approach to keep everyone aligned and informed.
Key Takeaways
- Preparation is critical: Create detailed contact lists, assign roles, and set up communication rules.
- Activate quickly: Notify the right people immediately and use secure channels for updates.
- Keep it clear: Use tiered messaging for different audiences (technical teams, executives, customers).
- Document everything: Log all decisions and communications for compliance and future reviews.
- Learn and improve: Conduct post-incident reviews to refine your protocols.
This checklist ensures your team communicates effectively, reduces damage, and maintains trust during a crisis.
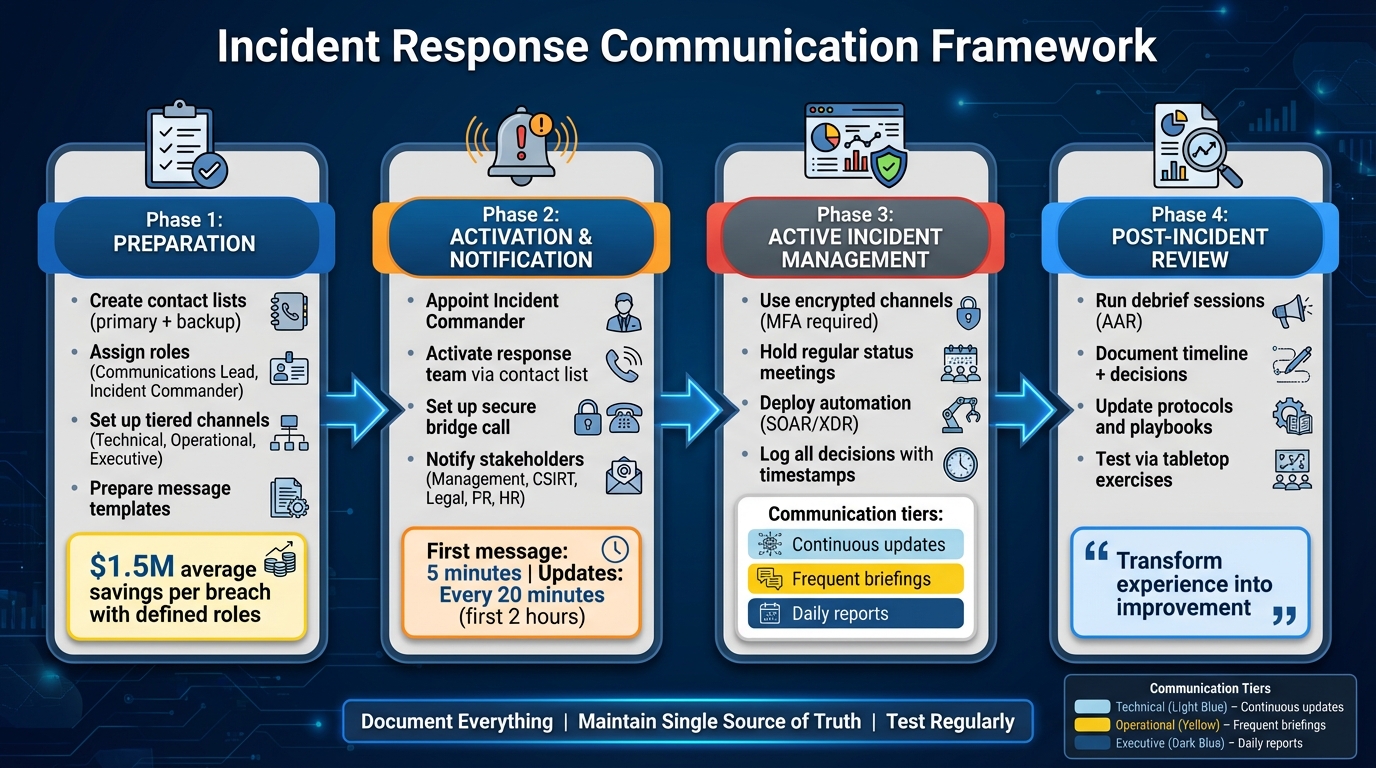
4-Phase Incident Response Communication Framework
Incident Communication Best Practices Guide
Preparation Phase: Setting Up Your Communication Framework
Building a strong communication framework is essential for handling incidents effectively, and the groundwork must be laid well before any crisis strikes. By documenting protocols in advance, you can act swiftly and decisively when time is of the essence. This involves creating detailed contact lists, assigning clear responsibilities, and establishing well-defined communication rules.
Create Complete Contact Lists
A well-prepared response starts with having comprehensive and easily accessible contact lists. These lists are crucial for preventing communication breakdowns during an incident. According to the NIST "Computer Security Incident Handling Guide" (SP 800-61), an effective contact list should cover a wide range of roles, including:
- Internal Technical Contacts: Key personnel like system administrators, network engineers, and application specialists who understand your infrastructure and platforms.
- Management and Coordination: An incident coordinator and someone who can translate technical issues into business terms for senior leadership.
- Business and Support Functions: Representatives from HR, Legal, PR, risk management, facilities management, and data owners.
- Customer-Facing Teams: Sales and customer service professionals who can manage external stakeholder concerns.
- External Partners: Points of contact for law enforcement, third-party vendors, and local emergency responders.
Each role should have both primary and backup contacts. Also, define who is authorized to engage law enforcement, as this decision can have significant public relations implications. Update the contact list regularly – at least once a year or whenever personnel changes occur. Review it with internal teams and local responders to ensure everyone is aligned.
"Incident response plans… lay out incident definitions, escalation requirements, personnel responsibilities, key steps to follow and people to contact in the event of an incident."
– Paul Kirvan, Independent Consultant
Assign Communication Roles and Responsibilities
Clearly defined roles help eliminate confusion during an incident. Start by assigning a Communications Lead to manage internal and external messaging and an Incident Commander to oversee decision-making.
Pre-assign representatives from key departments:
- Legal Counsel: To ensure compliance with regulations.
- HR: To address employee concerns and oversee internal investigations.
- PR Specialists: To handle media relations and public messaging.
Organizations with well-defined incident response roles reportedly save an average of $1.5 million per breach compared to those without.
"Defined incident management team roles ensure technical response, legal obligations, and communications are handled without confusion or delay."
– Sygnia Team
Ensure 24/7 contact details (email, SMS, VOIP) are recorded for all team members and their backups to avoid single points of failure. Specify who has the authority to activate the incident response plan and issue public statements. Visual tools, like stakeholder activation maps, can also improve coordination by showing when and how different teams should be engaged.
Set Up Internal and External Communication Rules
Establishing clear communication rules in advance prevents confusion and delays during an incident. Start by designating a central Incident Command Channel as the "Single Source of Truth" for validated updates. Use tiered communication channels to ensure the right information reaches the right audience:
- Technical Tier: For detailed updates shared among SOC teams and incident response specialists.
- Operational Tier: For concise impact summaries directed at department heads.
- Executive Tier: For high-level situational reports intended for the C-suite and board members.
Leverage secure, encrypted platforms with multi-factor authentication and integrated logging for all communication. Prepare pre-approved messaging templates and escalation flowcharts to streamline decisions. Maintain secure bridge calls between technical leads, legal counsel, and communications teams to ensure alignment.
Tailor your messages based on the audience: share technical specifics with responders, impact summaries with leadership, and reassuring updates with customers. Document key decisions to support post-incident reviews and meet compliance requirements, such as those mandated by GDPR or the SEC. Finally, plan for contingencies by setting up secondary communication channels in case primary systems are compromised.
These preparations ensure your organization is ready to respond quickly and effectively, maintaining clear and controlled communication during any incident.
Activation and Notification: Starting Incident Response Communication
When an incident strikes, having a solid communication plan in place is only the beginning. The real test lies in how quickly and accurately you can activate your team and notify stakeholders. The goal? To keep the response organized, minimize damage, and maintain trust. Here’s how to ensure your communication during an incident is both swift and effective.
Activate the Incident Response Team
The first step is to appoint an Incident Commander – a single person responsible for managing the response and making key decisions. This avoids the confusion that can arise when multiple people try to take charge. To keep everyone aligned, set up a secure, ongoing bridge call where technical leads, legal advisors, and communication teams can share verified updates.
Using your pre-prepared contact list, reach out to all team members immediately. If the primary contacts are unavailable, escalate to secondary or tertiary responders without delay. For sensitive discussions, create dedicated workspaces on encrypted platforms that are separate from regular corporate tools.
"In the first hour of a cyber incident, information moves faster than certainty." – Sygnia Team
Next, implement your tiered communication structure. Technical details should go to the SOC and response specialists, while summaries of the impact are sent to department heads. High-level updates should be shared with executives and board members. This ensures everyone gets the information they need without being overwhelmed by irrelevant details.
Once the team is up and running, the focus shifts to notifying both internal and external stakeholders.
Notify Key Stakeholders
After mobilizing your team, prioritize notifying key stakeholders. Senior management needs to be informed immediately to approve decisions and allocate resources. Your CSIRT team – comprising networking experts, system administrators, and incident coordinators – should already be engaged.
Depending on the nature of the incident, bring in additional departments. Legal and PR teams can address compliance and reputational concerns, while HR may need to step in if insider threats are suspected. Managers of affected business areas and data owners should assess operational impacts. Assign a liaison to translate technical updates into business terms for senior leaders.
"A well-designed incident response plan can be the crucial differentiator that lets an organization quickly contain the damage from an incident." – Paul Kirvan, Independent Consultant
External stakeholders also need careful handling. Regulators, law enforcement, customers, partners, and investors all require timely and accurate updates. Make sure it’s clear who is authorized to contact law enforcement, as this could lead to public disclosures that might affect your organization’s reputation. Use standardized playbooks for incidents like ransomware or data breaches to ensure you follow consistent and efficient notification steps.
Send Initial Incident Notifications
Your first notification should reassure stakeholders that the issue is being addressed and prevent unnecessary panic. Pre-approved templates can help speed up this process. Aim to send the initial message within 5 minutes of detection, followed by a second message within another 5 minutes. During the first two hours, provide updates every 20 minutes.
Keep the initial message concise. Confirm that the issue is under investigation, specify which services or products are affected, outline the severity, and let recipients know when to expect the next update. If needed, include immediate steps for mitigation or contingencies customers can take to protect their operations.
For high-priority stakeholders or customers with premium support contracts, supplement general notifications with personalized outreach through account teams or dedicated liaisons.
Finally, log every message and decision during this phase. Accurate timestamps and records are vital for internal reviews, regulatory compliance (like GDPR or SEC requirements), and external audits. This documentation will be a key resource for understanding what worked and what could be improved after the incident.
Active Incident Communication: Managing Real-Time Updates
When dealing with an incident, keeping communication clear, secure, and efficient is absolutely crucial. It’s a balancing act – speed and accuracy must go hand-in-hand, all while safeguarding sensitive information and maintaining alignment across teams.
Use Secure Communication Channels
Start by securing your communication platforms. Use end-to-end encrypted tools to shield sensitive data. Create dedicated workspaces specifically for incident management, separate from your usual corporate systems. This ensures operations can continue smoothly, even if your main network is compromised . Make sure all platforms require multi-factor authentication and adopt a least-privilege access policy.
"If an app is not end-to-end encrypted, deem it non-private." – Tess G., Stream.io
Establish a single, reliable source for all validated updates – whether it’s an Incident Command Channel or a secure dashboard. Then, tailor communication for different audiences:
- Technical teams need detailed telemetry and technical data.
- Operational teams require summaries of the incident’s impact and actionable steps.
- Executives benefit from concise, high-level reports.
It’s also wise to keep offline copies of your communication plans, just in case your digital systems fail. Once secure channels are set up, regular status meetings help ensure everyone stays on the same page.
Hold Regular Status Meetings
With secure communication in place, the next step is to establish a rhythm for status meetings. The frequency should reflect the urgency of the situation. For technical responders, persistent bridge calls allow for real-time updates and seamless handoffs. Operational teams need frequent briefings, while executives typically require daily updates or milestone-based reports.
| Communication Tier | Meeting Frequency | Primary Focus |
|---|---|---|
| Technical Tier | Continuous / Persistent | Detailed telemetry, indicators, remediation progress |
| Operational Tier | Frequent / As Needed | Impact summaries, departmental next steps |
| Executive Tier | Daily or Milestone-based | High-level situational reports, strategic decisions |
Source:
For executive briefings, keep it short and focused with standardized one-page situational reports. Measure how quickly decisions are made after incidents are confirmed – this metric highlights the efficiency of your communication strategy. Every step, from containment to recovery, should be logged with timestamps to maintain accountability.
Use Automation Tools for Alerts and Tracking
Automation can be a game-changer during incident response. Platforms like Security Orchestration, Automation, and Response (SOAR) can handle repetitive tasks such as isolating compromised devices, blocking malicious IPs, or revoking credentials. Some Extended Detection and Response (XDR) systems can deploy across thousands of endpoints in just a couple of hours.
Create automated playbooks tailored to specific attack types. For instance, a ransomware attack will require different steps than a DDoS incident. These playbooks should integrate seamlessly with your security tools, ensuring consistency in execution. Treat generative AI as a helpful assistant – use its recommendations but always have human analysts review them before acting.
"Automation speeds up incident response, ensures consistent execution of remediation steps, and frees security personnel to prioritize complex incident analysis." – Cynet
Keep a detailed log of all actions, whether automated or manual, complete with timestamps. These records are vital for forensic investigations and compliance with regulations like GDPR or SEC disclosure rules . Lastly, design your automation and communication tools with built-in redundancies to ensure they remain operational, even during a system-wide compromise.
sbb-itb-760dc80
External Communications: Managing Public and Stakeholder Engagement
Once internal activation and notifications are underway, the focus shifts to external communications. This step is crucial for maintaining your reputation and preserving stakeholder trust. When an incident becomes public, every word matters. Your response can either shield your reputation or make the situation worse. Acting swiftly, maintaining consistency, and adhering to legal guidelines are all essential.
Prepare and Approve Key Messages
Speed and accuracy are everything – aim to release your first external communication within five minutes. To make this possible, have pre-approved templates ready ahead of time. These templates should cover media statements, customer notifications, social media posts, and Q&A documents tailored to various scenarios. Each template should be designed specifically for its audience, whether that’s the media, customers, or the general public, ensuring the right message reaches the right people.
It’s equally important to establish a clear approval process before a crisis occurs. Legal and HR teams need to review every statement to ensure compliance and limit liability. Meanwhile, C-level executives should sign off to align the messaging with broader business objectives, and PR specialists can help fine-tune the tone and narrative. A good example of why this matters comes from July 2023, when UK-based Capita initially referred to a disruption as an "IT issue" before later clarifying it was a "cyber incident." This shift in terminology significantly influenced public perception and their communication strategy.
"Whatever you do: don’t attempt to ‘spin’ a crisis. If a post seems showy or calculated, it can damage your relationship with your customers." – Hootsuite
Every message should hit specific points: acknowledge the incident and its ongoing investigation, outline the affected products or regions, provide actionable steps for stakeholders (like resetting passwords), share the current mitigation efforts, and specify when the next update will come. Tailor the level of technical detail based on the audience – partners may need in-depth information, while customers typically prefer concise summaries. This structured approach ensures you’re prepared to address investors, regulators, and customers with clarity.
Inform Investors and Regulators
Once your key messages are approved, shift your focus to financial and regulatory stakeholders. Direct communication with these groups is non-negotiable. Before a crisis occurs, identify the notification requirements specific to your industry and location. For publicly traded companies, consider implementing trading blackouts during incidents that could affect stock value. This helps prevent insider trading accusations and reassures shareholders.
Involve legal experts from the outset, as incidents can lead to regulatory penalties or even criminal charges. A recent example is password manager LastPass, which was fined £1.2 million by the UK’s Information Commissioner’s Office in October 2023 for security lapses. Coordinate with law enforcement when necessary, and stick to factual updates – avoid speculation until investigations are complete.
"The hours and minutes immediately after an incident are critical in media relations, and the financial stakes and risks only increase with the passage of time." – Brittany Manley, Software Engineering Institute
Handle Customer-Facing Channels
During a crisis, customers will have countless questions. Set up dedicated channels like status pages, support lines, or messaging apps to provide continuous updates. Aim to refresh these updates at least every 20 minutes during the first two hours.
Keep a close eye on social media using tracking tools to quickly address any misinformation. For instance, after a major ransomware attack in October 2023, the British Library released a detailed "lessons learned" report. This effort not only demonstrated transparency but also contributed to broader industry resilience. Expand your call center and email support capabilities as needed, and direct customers to trusted resources like the NCSC or CERT for additional guidance.
"Transparency helps build trust and credibility with stakeholders. Commit to transparent communication with your stakeholders, and provide timely updates on the incident, its impact and your response." – NCSC
Post-Incident Review: Documenting and Improving Communication
Once the immediate crisis is under control, it’s time to shift gears and focus on what can be learned. This phase is all about dissecting the response, analyzing communication efforts, and figuring out how to do better next time. After-action reviews (AARs) are essential for identifying what went well, what didn’t, and why. The ultimate goal? To ensure your team is even more prepared for the next challenge.
Run Debrief Sessions
Hold a thorough debrief as soon as possible after the incident. Gather everyone involved – Incident Commander, Communications Lead, Executive Liaison, and key stakeholders. The focus should be on measurable performance indicators like the accuracy of escalations, how quickly decisions were made, and the effectiveness of stakeholder communication.
Review whether updates shared during the incident came exclusively from the Incident Command Channel and whether any misinformation was swiftly addressed. Assess how well each team member fulfilled their responsibilities and identify any bottlenecks or gaps that slowed the response. For companies operating across multiple regions, evaluate how well communication was coordinated across time zones and locations. These discussions provide the insights needed to update protocols and improve future performance.
"The real work begins when an incident or simulation ends. The after-action review (AAR) transforms experience into improvement, identifying what worked, what didn’t, and why." – Sygnia Team
Document All Communication Activities
Create a detailed timeline that logs every decision and action taken during the incident. This serves multiple purposes: ensuring compliance with regulations like GDPR and SEC disclosure rules, supporting forensic investigations, and providing evidence for any legal reviews that may arise.
Each decision should be logged with a timestamp and the name of the person responsible. This level of detail is critical for adhering to frameworks like ISO 27035 and maintaining a clear chain of custody for evidence. To make this process seamless, schedule regular intervals for logging updates – hourly during active incidents is a good rule of thumb . Real-time documentation makes it easier to refine communication strategies later.
Update Communication Protocols
Take the lessons learned from your debrief sessions and use them to improve your playbooks, escalation charts, and message templates. If you discovered delays in communication between the SOC and executive teams, consider implementing "bridge calls" – secure, ongoing sessions designed to keep technical, legal, and communications teams aligned in real time. If primary responders were unavailable, update your contact lists and escalation hierarchies to prevent future gaps.
Evaluate your incident dashboard or central hub to see if it effectively served as the go-to source for information. If executives found the situational reports too technical, adjust the template to focus more on business impacts. Finally, test all updated protocols through tabletop exercises or cyber range simulations to ensure they work seamlessly in practice .
"The first time the plan is tested should not be in the middle of a cybersecurity incident." – Brittany Manley, Software Engineering Institute
Conclusion
Handling incident response effectively starts with a clear communication plan, even when information is incomplete. The checklist provided walks you through every critical step – from creating contact lists and assigning roles during preparation to managing updates in real time and conducting thorough post-incident reviews. Each phase connects seamlessly to the next, offering a solid framework that keeps your team on the same page when time is of the essence.
Preparation and practice are key to staying in control. Regular tabletop exercises can help uncover gaps in communication and sharpen your team’s readiness. Testing your protocols in realistic scenarios is the only way to ensure they’ll perform when it matters most.
Frequent reviews are equally important for keeping your framework up to date. Use incident data to establish measurable goals, like escalation speed and decision-making accuracy, and make sure to update your playbooks immediately after every incident.
Failures in communication often come down to human error – a missed message or a delayed notification can quickly worsen a crisis. To prevent this, embed clear protocols into your plans, maintain version-controlled templates, and rehearse restoration procedures regularly. By learning from each incident, your team will build stronger habits and improve its overall crisis response.
Take the time to review your protocols, run a tabletop exercise, refresh your contact lists, and ensure everyone knows their role. The organizations that respond most effectively aren’t necessarily the ones with the fanciest tools – they’re the ones that have practiced their communication strategy until it becomes second nature.
FAQs
What are the main roles in an incident response communication team?
An effective incident response communication team is built around several key roles, each contributing to clear, accurate, and coordinated messaging during a cybersecurity incident:
- Incident Response Lead: This person oversees the entire response process, assigns tasks, and ensures the plan is carried out efficiently.
- Communications Lead: Responsible for managing both internal and external messaging, ensuring employees, executives, customers, and media receive consistent and clear information.
- Legal Counsel: Provides advice on compliance, liability, and regulatory requirements. They also review all communications to ensure they align with legal standards.
- Technical Lead: Focuses on the technical side of the incident, handling investigation, containment, and recovery. Their insights are crucial for crafting accurate and informed messaging.
- Executive Sponsor: Offers strategic oversight, allocates necessary resources, and communicates critical decisions to leadership and external partners.
- External Liaison: Acts as the point of contact for third-party vendors, law enforcement, and regulators, ensuring timely and accurate updates are shared.
Each role plays a vital part in ensuring the response is thorough, legally sound, and effectively communicated to all relevant stakeholders.
How can organizations maintain secure communication during a cybersecurity incident?
To maintain secure communication during a cybersecurity incident, it’s crucial to rely on encrypted channels. This could mean using secure messaging apps, S/MIME-signed emails, or specialized incident-response platforms. Communication should always adhere to a structured plan, outlining clear roles and responsibilities. Tools like the Traffic Light Protocol (TLP) can help manage how information is shared and who has access to it.
Regular testing and drills play a vital role in ensuring the reliability of communication tools. These exercises confirm that encryption keys are current and that backup options, such as out-of-band phone lines, are ready to use if needed. A communication lead should oversee updates to maintain consistency and accuracy, with all correspondence carefully logged and archived for accountability.
Keeping up with best practices – like adopting zero-trust principles and managing encryption keys securely – ensures your protocols remain effective. A well-prepared and practiced communication plan guarantees that confidentiality, integrity, and availability are upheld during an incident.
Why are post-incident reviews critical for incident response teams?
Post-incident reviews play a crucial role in evaluating what worked, pinpointing areas for improvement, and fine-tuning response strategies. These reviews allow teams to adjust their processes, address security vulnerabilities, and better prepare for future challenges.
By diving deep into the details of an incident, teams can turn lessons into actionable steps, reducing the chances of similar problems and bolstering the organization’s ability to handle future incidents.

