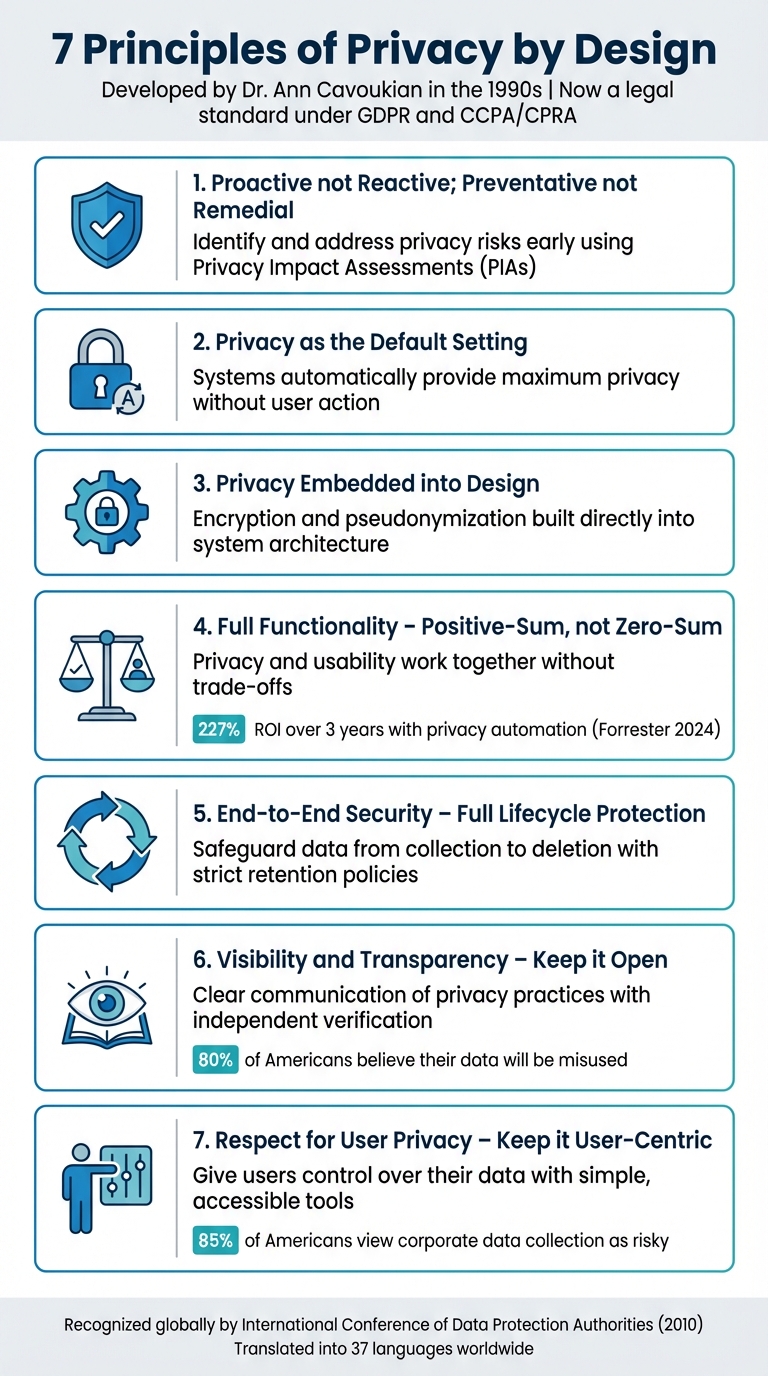
Privacy by Design (PbD) ensures privacy is built into systems from the start. Developed by Dr. Ann Cavoukian in the 1990s, this approach focuses on preventing privacy risks rather than fixing them later. It’s now a legal standard under regulations like GDPR and CCPA/CPRA. Here’s a quick breakdown of the 7 core principles:
- Prevent Problems Before They Happen: Identify and address privacy risks early using tools like Privacy Impact Assessments (PIAs).
- Privacy as the Default Setting: Systems should automatically provide maximum privacy without user action.
- Privacy Built Into Design: Embed privacy measures like encryption and pseudonymization directly into system architecture.
- Full Functionality Without Trade-Offs: Prioritize both privacy and usability for a balanced approach.
- Protection Throughout the Data Lifecycle: Safeguard data from collection to deletion with strict retention policies and security measures.
- Transparency and Open Operations: Clearly communicate privacy practices and allow independent verification.
- User-Centered Privacy Approach: Give users control over their data with simple, accessible tools and clear consent mechanisms.
7 Principles of Privacy by Design Framework
Privacy by Design | 7 Key Principles of the Privacy-by-Design Approach | How to Ensure Privacy?
1. Prevent Problems Before They Happen
The core idea here is to act ahead of time, not after issues arise. By identifying and addressing privacy risks during the planning phase, you can save time, money, and effort – while also safeguarding your reputation and earning user trust. This forward-thinking approach lays the groundwork for effective privacy measures.
"Privacy by Design comes before-the-fact, not after." – Dr. Ann Cavoukian, Former Information and Privacy Commissioner for the Province of Ontario
One key step is conducting a Privacy Impact Assessment (PIA) right at the start of a project. This allows you to map out how data will flow and pinpoint potential vulnerabilities. Bringing together cross-functional teams to create a detailed data flow table can help highlight where sensitive information travels and where it might be at risk.
From the beginning, you should also implement tools like encryption, pseudonymization, and anonymization to protect data. Classify information based on its sensitivity – such as medical or financial records, which require stricter safeguards. Taking these steps early not only minimizes risks but also avoids costly fixes down the line.
2. Privacy as the Default Setting
The idea here is simple yet powerful: privacy should be automatic. Users shouldn’t have to tweak settings or take extra steps to protect their personal information. From the moment someone opens your app or visits your website, the strictest privacy settings should already be in place. This ensures that personal data stays protected without requiring any action from the user.
"Privacy by Design advances the view that the future of privacy cannot be assured solely by compliance with regulatory frameworks; rather, privacy assurance must ideally become an organization’s default mode of operation." – Ann Cavoukian, former Information and Privacy Commissioner of Ontario
To make this a reality, organizations need to take proactive steps. Start by collecting only the bare minimum amount of data necessary for a specific purpose. Systems should be designed to default to using non-identifiable data whenever possible. Automated policies should delete or anonymize data once it’s no longer needed. On top of that, encryption, strict access controls, and limiting third-party data sharing to only what’s essential should be the norm.
This approach isn’t just good practice – it’s also a legal requirement in some cases. For example, Article 25 of the GDPR enforces "Data Protection by Design and by Default." By adopting these measures, organizations not only comply with regulations but also take the responsibility of privacy protection off users’ shoulders. This builds trust and reduces the overwhelming task of managing privacy settings.
3. Privacy Built Into Design
Privacy isn’t something you can tack on later – it has to be part of the blueprint from the very beginning. This means weaving data protection directly into the architecture of your IT systems and the core of your business practices .
Start by making features like encryption, authentication, and pseudonymization standard components of your system architecture. But don’t stop there – technical safeguards need to be paired with organizational measures, such as clear internal policies and strict access controls . Together, these steps lay the groundwork for effective privacy risk management.
"Privacy measures are embedded into the design and architecture of IT systems and business practices. These are not bolted on as add-ons, after the fact." – Dr. Ann Cavoukian, Creator of Privacy by Design
In today’s climate, where trust is hard to earn, embedding privacy into your design isn’t just the right thing to do – it’s smart business.
Every project should kick off with a Privacy Impact Assessment (PIA) or a Data Protection Impact Assessment (DPIA) to spot and address risks early on . Commit to a privacy-first approach and regularly test your systems for vulnerabilities to ensure your safeguards stay strong .
4. Full Functionality Without Trade-Offs
The concept of Privacy by Design flips the traditional "either-or" mindset on its head. In the past, organizations often believed they needed to compromise privacy to achieve stronger security, better user experiences, or more features. Privacy by Design, however, embraces a "win-win" philosophy, proving that privacy and functionality can thrive together. By embedding privacy as a fundamental design principle, you not only protect user data but also enhance the overall quality and reliability of your product.
A 2024 study by Forrester Consulting revealed a 227% return on investment (ROI) over three years for companies implementing privacy automation to streamline governance and consent processes. This underscores that privacy isn’t just about compliance – it’s a powerful competitive edge.
"Those who work to integrate privacy into every design element seamlessly take a positive-sum approach. These innovators will see their brands grow in a world where privacy is increasingly a market mover, not just an issue of legal compliance."
– Kadi Coult Wharton, Director Privacy & Data Governance Content, OneTrust
Encourage your team to create solutions where privacy and functionality complement each other. Every design decision should prioritize privacy without sacrificing usability or performance. When done right, this approach not only builds customer trust but also fosters innovation. It lays the groundwork for embedding privacy throughout the entire data lifecycle, ensuring long-term success.
sbb-itb-760dc80
5. Protection Throughout the Entire Data Lifecycle
Safeguarding privacy isn’t a one-time task – it’s a commitment that spans from the moment data is collected to when it’s deleted. This requires a robust, end-to-end security approach to ensure personal information remains confidential, intact, and accessible only to authorized individuals at every stage of its lifecycle. Essentially, it’s about embedding the principles of Privacy by Design into every aspect of data management.
"Privacy by Design ensures cradle to grave, secure lifecycle management of information, end-to-end."
– GPS by Design Centre
The growing lack of trust in how data is handled makes these protections more critical than ever. To address these concerns, organizations must adopt rigorous measures throughout the entire data lifecycle.
Start by mapping your data flows to gain a clear understanding of how information moves – from collection to use, storage, and eventual deletion. Each dataset’s sensitivity level should guide the safeguards applied. For example, highly sensitive data might require encryption during storage, role-based access controls during processing, and secure deletion methods once it’s no longer needed . It’s also crucial to implement strict retention policies, ensuring data is only kept for as long as it serves its original purpose.
Ongoing vigilance is key. Regular audits and continuous monitoring by a dedicated team can help identify and address new threats as they arise, ensuring your protections evolve alongside the risks.
6. Transparency and Open Operations
Trust is built through actions that people can see and verify – not through lofty promises. To earn and maintain trust, organizations must clearly communicate their privacy practices without hiding behind complicated legal jargon. Being open about operations is fundamental to fostering trust that lasts.
A staggering 80% of Americans believe their data will be used for purposes beyond what was initially stated. This highlights a significant trust gap that can only be addressed with genuine transparency. Companies need to show, not just tell, that they treat data protection as a responsibility, not a mere regulatory requirement.
"Visibility and transparency – keep it open. Remember to trust but verify."
– Ann Cavoukian, Ph.D., Former Information and Privacy Commissioner of Ontario
Real-world examples show how transparency can build trust. For instance, Signal Messenger has an entirely open-source codebase, which allows independent experts to continuously audit its end-to-end encryption. Similarly, the Wikimedia Foundation publishes detailed annual reports about its finances and resource use, earning the Platinum Seal of Transparency from Candid and top ratings from Charity Navigator for its openness.
To make transparency work in practice, start by writing privacy notices in plain language that your audience can easily understand. Create a straightforward process for users to submit privacy-related concerns and ensure they receive meaningful responses. Open standards or third-party audits can also help verify your privacy practices. Most importantly, inform users about why you’re collecting their data at or before the moment of collection. Avoid burying this information in lengthy terms and conditions that no one reads. By being upfront, you reinforce the proactive privacy measures discussed earlier and show users that their trust is well-placed.
7. User-Centered Privacy Approach
This principle focuses on putting people first in every privacy-related decision. Instead of treating users as passive participants whose data is simply processed, this approach gives them the tools and control to actively manage their information at every stage of its lifecycle.
Research shows that most Americans view data collection as more of a risk than a benefit, highlighting the importance of giving users the ability to manage their personal data effectively. A user-centered approach is key to building trust. By designing privacy controls around the user, organizations can ensure that the proactive measures mentioned earlier extend throughout the entire data lifecycle.
"Human-machine interfaces to be human-centered, user-centric and user friendly so that informed privacy decisions may be reliably exercised."
– Ann Cavoukian, Ph.D., Former Information and Privacy Commissioner for Ontario
To achieve this, companies need to remove confusing consent mechanisms, like pre-checked boxes, and provide clear, detailed options that make it easy for users to withdraw consent when needed. Self-service tools should allow users to access their data, verify its accuracy, and request changes or deletions – these features should be core to the system, not last-minute additions. Privacy settings should be as simple to locate and use as the main features of the product, not hidden in obscure sub-menus.
Privacy controls should be built into the design from the start. Use just-in-time notifications that clearly explain why data is being collected and how it will be used, right at the moment of collection. Additionally, offer accessible channels for complaints and resolutions, ensuring users feel their concerns will be addressed meaningfully. Giving users this level of control not only reinforces privacy-first principles but also builds stronger trust in your systems.
How to Implement Privacy by Design
Start by conducting Data Protection Impact Assessments (DPIAs) during the requirements gathering phase. This helps you quickly pinpoint and address privacy risks early, making it easier to implement changes and keep costs down. Work with your ICT teams to extract privacy requirements from relevant software standards and U.S. laws. Use tools like traceability matrices to weave these requirements into design elements, such as role-based access controls, ensuring privacy is baked into the system from the start.
Once risks are identified, focus on building strong defenses. During the planning stage, put in place Technical and Organizational Measures (TOMs) like pseudonymization, encryption, anonymization, and user authentication. These measures protect data throughout its lifecycle – from collection to disposal. Systems should also be configured to provide maximum privacy protection by default, so users get the highest level of privacy without needing to adjust settings.
"Data protection by design is about considering data protection and privacy issues upfront in everything you do." – Information Commissioner’s Office (ICO)
Incorporate privacy strategies such as "Minimize and Separate", "Hide and Abstract," and "Inform and Control." These approaches limit data access, prevent misuse, and give users more control over their information. Collect only the data you absolutely need and present privacy policies in plain, easy-to-understand language. This not only enhances data security but also ensures compliance with legal and regulatory standards.
To stay ahead, leverage frameworks like the NIST Privacy Framework to integrate privacy into enterprise risk management. This also helps align with evolving U.S. regulations, such as the June 6, 2025, Executive Order on Sustaining Select Efforts to Strengthen the Nation’s Cybersecurity. For ongoing guidance, tools like Cyber Detect Pro offer expert insights and updates on cybersecurity best practices. By following these steps, you can effectively operationalize Privacy by Design principles while staying compliant and prepared for emerging challenges.
Conclusion
Privacy by Design goes far beyond meeting compliance requirements – it’s about building trust at every level of business interaction. When companies prioritize privacy from the outset, they avoid the expensive and often chaotic process of retrofitting security measures after launch. More importantly, they demonstrate to customers, partners, and regulators that protecting personal information is a fundamental priority. This proactive mindset aligns perfectly with the strategies outlined earlier.
Consider this: 85% of Americans view corporate data collection as risky, and 81% are uneasy about how AI uses their data. That’s a lot of skepticism. But organizations that embrace Privacy by Design principles can transform this doubt into a competitive edge. As Dr. Ann Cavoukian, the creator of Privacy by Design, famously said:
"Privacy assurance must ideally become an organization’s default mode of operation"
The benefits go beyond trust. Companies that prioritize privacy often find they can simplify vendor security reviews. By collecting only the data they truly need and safeguarding it throughout its lifecycle, these organizations reduce their exposure to potential breaches. This approach not only minimizes risks but also strengthens their position when negotiating major deals.
The global endorsement of Privacy by Design speaks volumes about its importance. In October 2010, regulators at the International Conference of Data Protection Authorities and Privacy Commissioners unanimously recognized it as a cornerstone of privacy protection. Since then, the framework has been translated into 37 languages, underscoring its relevance in today’s interconnected world. This recognition highlights a universal truth: privacy protection is a shared responsibility that crosses borders and industries.
FAQs
How does Privacy by Design relate to GDPR and CCPA/CPRA regulations?
Privacy by Design plays a key role in the GDPR, requiring businesses to embed data protection by design and by default into their operations. This involves building technical and organizational safeguards – like Data Protection Impact Assessments (DPIAs) – directly into systems and processes from the outset to ensure compliance.
Although Privacy by Design isn’t specifically required under the CCPA or CPRA, its principles align closely with these laws’ focus on safeguarding personal data and empowering individuals with greater control over their information. Embracing Privacy by Design not only helps businesses stay compliant but also strengthens customer trust.
How can I apply Privacy by Design principles to a new project?
To weave Privacy by Design (PbD) into your project from the start, it’s crucial to define the scope and set clear privacy goals early on. Make sure these objectives – like limiting data collection – align with your business needs. Create a map of how personal data will move through your system, classify its sensitivity levels, and conduct a Privacy Impact Assessment (PIA) to uncover and address any risks.
Bring PbD principles to life by anticipating privacy challenges upfront. Set privacy-friendly defaults, incorporate controls such as encryption, and design features that strike a balance between functionality and privacy. Protect data throughout its entire lifecycle, and offer users clear, simple ways to manage their information. Don’t forget to document your privacy measures, keep them under regular review, and provide training for stakeholders to ensure everything stays on track.
For expert guidance and actionable advice, Cyber Detect Pro can help you implement these strategies, building projects that prioritize both security and privacy from day one.
How can organizations ensure both privacy and functionality work together effectively?
Organizations can strike a balance between privacy and functionality by viewing them as complementary goals rather than conflicting ones. The idea behind Full Functionality – Positive-sum, not Zero-sum is that systems can be designed to protect user privacy while still meeting business objectives – no compromises required. By integrating privacy into the very foundation of product design and making it the default, companies can safeguard user data while delivering a smooth, user-friendly experience.
There are practical ways to achieve this. For instance, leveraging tools like encryption or differential privacy can enhance data protection. Modular features, where users can adjust privacy settings without disrupting the overall functionality, are another effective approach. Additionally, implementing end-to-end security ensures data remains protected throughout its lifecycle. Transparency also plays a huge role – keeping users informed about how their data is being used fosters trust and confidence.
For businesses looking for expert advice on merging privacy with usability, Cyber Detect Pro provides valuable insights to help maintain security without sacrificing user experience.

