When security flaws are discovered, researchers face a tough choice: Should they work with vendors privately to fix the issue (Coordinated Disclosure) or share all details immediately (Full Disclosure)? Both approaches have their pros and cons, impacting users, vendors, and attackers differently.
- Coordinated Disclosure (CVD): Researchers collaborate with vendors and sometimes third parties to fix vulnerabilities before public announcements. This minimizes risks for users by aligning public disclosure with available patches or mitigations.
- Full Disclosure: Vulnerability details are made public immediately, even without a fix. While this informs users quickly, it also gives attackers the same information, potentially putting systems at greater risk.
The choice depends on the situation, but CVD is often preferred to reduce harm. Governments, like the EU under the NIS2 Directive, are formalizing CVD practices to ensure better security coordination. However, Full Disclosure still plays a role in holding vendors accountable when they delay fixes.
Quick Comparison
| Factor | Coordinated Disclosure (CVD) | Full Disclosure |
|---|---|---|
| Goal | Release info with a fix/mitigation | Inform public immediately |
| Timing | Follows a planned timeline | Released immediately |
| Collaboration | High, involves multiple parties | Low, researcher-led |
| User Impact | Lower risk, actionable solutions | Higher risk, no immediate fix |
| Vendor Involvement | Vendors notified privately | Vendors may learn with public |
Both methods have strengths and challenges, but clear policies, communication, and trust between researchers and vendors are key to managing vulnerabilities effectively.
Coordinated Disclosure vs Full Disclosure: Key Differences in Vulnerability Management
Navigating The Coordinated Vulnerability Disclosure Landscape By Edwin Foudil (2023)
What Are Coordinated Disclosure and Full Disclosure?
These two approaches reflect different philosophies on how security researchers, vendors, and users handle vulnerabilities throughout their lifecycle.
Coordinated Disclosure Explained
Coordinated Vulnerability Disclosure (CVD) is a process where researchers, vendors, and sometimes third-party coordinators work together privately to address a security flaw before making it public. The CERT Coordination Center defines CVD as "the process of gathering information from vulnerability finders, coordinating the sharing of that information between relevant stakeholders, and disclosing the existence of software vulnerabilities and their mitigations to various stakeholders including the public".
Here’s how it typically works: When a researcher identifies a vulnerability, they notify the vendor securely. The vendor then validates the issue, determines its priority, and develops a patch or workaround. Once the patch is ready – or after a pre-agreed deadline – the vulnerability details are made public. This method limits the time attackers have to exploit the issue, as defenders are already equipped with solutions when the information is released.
You might also hear the term "responsible disclosure" used in place of CVD. However, many organizations, including CERT/CC, have moved away from this term. Why? Because the word "responsible" can lead to disagreements and hinder cooperation. As the CERT Guide to CVD notes:
The sticking point comes down to the fact that what constitutes responsible behavior is a matter of opinion that is always framed within the values of whoever is using the term.
For instance, vendors might argue that revealing a vulnerability before a patch is ready is "irresponsible", while researchers could claim that a vendor’s slow response is equally "irresponsible." By adopting "coordinated disclosure", the focus shifts to collaboration rather than subjective judgments.
Full Disclosure Explained
Full Disclosure, on the other hand, takes a completely open approach. Full Disclosure involves sharing all technical details of a vulnerability immediately after discovery – sometimes including proof-of-concept code that demonstrates how the flaw can be exploited. In this approach, there’s no waiting for a patch, and vendors are often informed at the same time as the public – or even afterward.
The philosophy behind Full Disclosure centers on transparency and urgency. Advocates believe that users deserve to know about vulnerabilities affecting their systems, even if no fix is available yet. With this information, organizations can take temporary steps – like changing configurations, isolating networks, or disabling risky features – to minimize their exposure.
At the same time, publicizing these details puts pressure on vendors to act quickly, as their reputation and customer trust are on the line. However, this openness comes with a trade-off: attackers also gain immediate access to the vulnerability details, potentially exploiting it before defenses are in place.
Each approach has its own ethical and practical challenges, shaping how the cybersecurity world navigates the balance between transparency, security, and accountability. The differences between these philosophies become even more pronounced when comparing their real-world impacts.
How Vulnerability Disclosure Practices Have Changed Over Time
Over the years, the way we handle security vulnerability disclosure has transformed significantly. What started as a reactive and often contentious process has matured into a more organized and cooperative effort that balances openness with security.
How Full Disclosure Became Popular
The rise of Full Disclosure was a direct reaction to how vendors used to handle – or rather, ignore – security vulnerability reports. Back then, many companies didn’t have clear processes for receiving these reports. Worse, researchers were often met with suspicion, hostility, or outright dismissal when they tried to report flaws privately.
Faced with such roadblocks, researchers turned to public disclosure as a way to force action. This wasn’t just about holding vendors accountable; it was also about informing users who were unknowingly exposed to risks. Without public awareness, users had no way to protect themselves while waiting for vendors to acknowledge and fix critical issues. Full Disclosure became a tool to empower users to make informed decisions about their security, even if it meant airing vulnerabilities publicly.
The tension of this era is well captured in the CERT Guide to CVD:
The vendors cry, "Disclosing a vulnerability without an available patch is not responsible!" "Not fixing this vulnerability quicker is not responsible!" the finders retort
- CERT Guide to CVD
Public pressure worked. Vendors, worried about the reputational damage from exposed flaws, were compelled to act faster. However, researchers argued that secrecy wasn’t the answer – attackers could find and exploit these vulnerabilities regardless of whether they were publicly disclosed or not.
Why the Industry Shifted to Coordinated Disclosure
While Full Disclosure had its merits, its drawbacks became increasingly clear. On the one hand, publicizing vulnerabilities without a fix gave attackers immediate opportunities to exploit them. On the other hand, keeping vulnerabilities under wraps left users defenseless, as they had no information to protect themselves.
This led to the adoption of Coordinated Disclosure – a more structured and collaborative approach. Several developments helped this shift gain traction. Neutral organizations like the CERT Coordination Center played a crucial role in formalizing these practices. By the early 2000s, frameworks such as the 2002 "Responsible Vulnerability Disclosure Process" by Christey and Wysopal and the 2004 National Infrastructure Advisory Council framework laid the groundwork for coordinated practices.
The main goal of Coordinated Disclosure was to minimize the time attackers had to exploit vulnerabilities. This approach ensures that vulnerability details are released in sync with available fixes or mitigations, offering transparency while prioritizing user protection. The adoption of coordinated policies became widespread, with the European Union implementing such measures across its Member States as of October 17, 2024.
Another key realization was that a vendor’s responsiveness to vulnerabilities mattered more than the sheer number of issues discovered. As the CERT Guide to CVD puts it:
The number of vulnerabilities found in a vendor’s products is less valuable as an indicator of the vendor’s security stance than the consistency of its response to vulnerabilities in a comprehensive and timely manner.
This evolution has shaped the balanced approach to vulnerability disclosure that we see today, where collaboration and transparency go hand in hand.
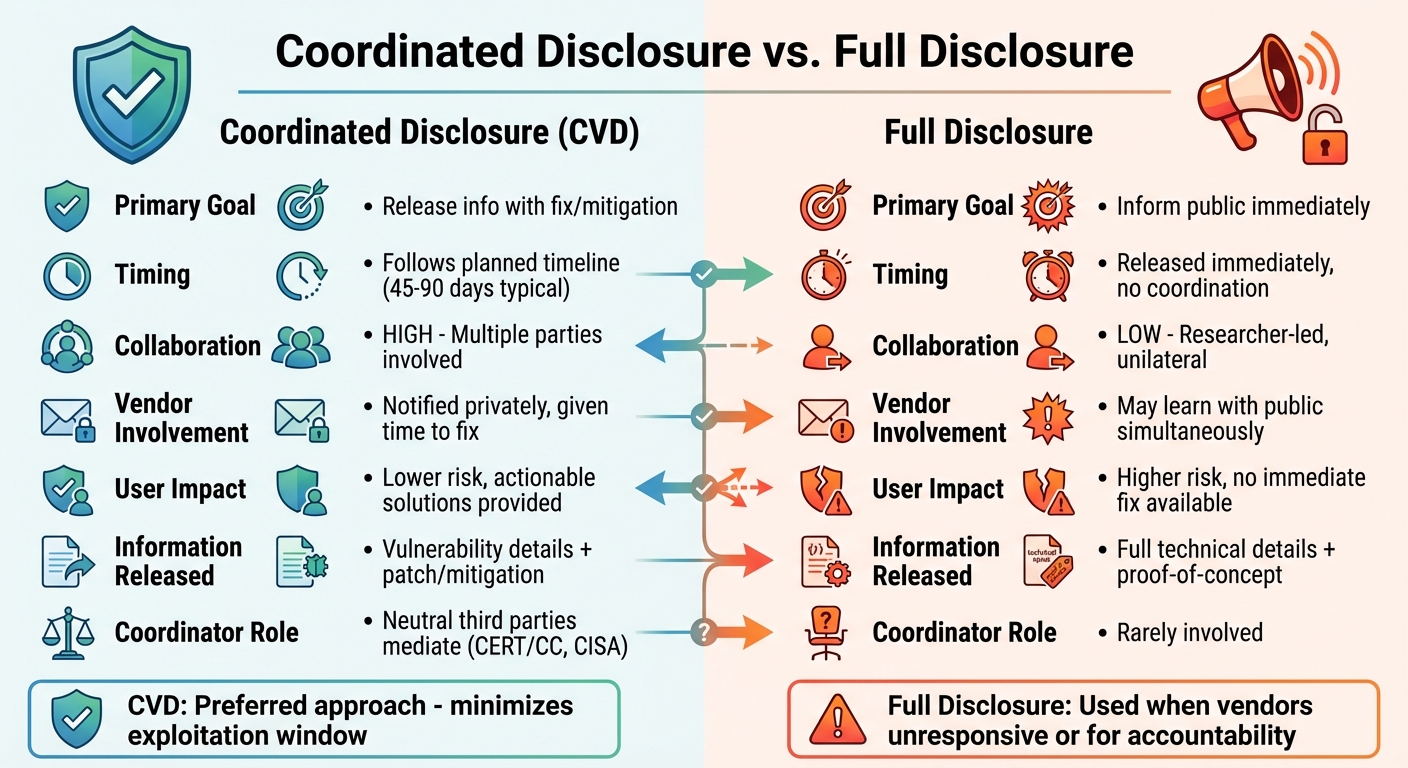
Coordinated Disclosure vs. Full Disclosure: Side-by-Side Comparison
Let’s take a closer look at how Coordinated Disclosure and Full Disclosure differ in terms of timing, collaboration, and the impact they have. Coordinated Disclosure follows a planned timeline, giving vendors time to develop patches or fixes. On the other hand, Full Disclosure shares vulnerability details right away, regardless of whether a solution is available. These contrasting approaches highlight key trade-offs that affect researchers, vendors, and users.
Stakeholder involvement is a major point of distinction. Coordinated Vulnerability Disclosure (CVD) is a group effort, where researchers, vendors, and often neutral parties like CERT/CC or CISA work together to address the issue. In contrast, Full Disclosure is typically a solo decision by the researcher, often triggered by a lack of response from the vendor.
The risk to users also varies significantly. With CVD, users get both the vulnerability information and guidance on how to protect their systems – usually in the form of a patch or workaround. Full Disclosure, however, informs users about the threat but often leaves them without an immediate fix. In some cases, organizations like CISA may step in to disclose vulnerabilities if vendors fail to act within a reasonable timeframe – often around 45 days after initial contact – balancing the need for public awareness with reducing harm. These differences underline the unique benefits and challenges of each method.
Comparison Table: Main Differences
| Factor | Coordinated Disclosure (CVD) | Full Disclosure |
|---|---|---|
| Primary Goal | Minimize risk by sharing information alongside a mitigation | Inform the public immediately, regardless of patch status |
| Timing | Follows a negotiated timeline with an embargo period | Released immediately or without coordination |
| Information Released | Vulnerability details plus mitigation advice or a patch | Detailed technical data, often with proof-of-concept |
| Collaboration Level | High; involves researchers, vendors, and facilitators like CERT/CC or CISA | Low; typically a unilateral researcher action |
| Vendor Involvement | Vendors are notified privately and given time to develop a fix | Vendors often learn of the issue at the same time as the public |
| User Impact | Users receive actionable steps to secure their systems | Users are informed but may lack an immediate solution |
| Risk to End Users | Lower; information and fixes are released together | Higher; users are alerted without a corresponding patch |
| Coordinator Role | Neutral third parties mediate and facilitate communication | Rarely involved |
sbb-itb-760dc80
Coordinated Disclosure: Benefits and Drawbacks
Why Coordinated Disclosure Works
The Coordinated Vulnerability Disclosure (CVD) framework offers a structured approach to handling security vulnerabilities, aiming to reduce risks by aligning disclosure with available fixes or mitigations. When a vulnerability is reported, users are provided with clear, actionable steps – whether it’s applying a patch, using a workaround, or following mitigation instructions – helping to safeguard their systems.
Having a well-defined CVD policy creates transparency and sets clear expectations, making the process smoother and fostering trust between stakeholders. For vendors, a timely and organized response not only addresses security issues but can also serve as a public relations advantage, showing they are proactive and prepared. The CERT Coordination Center, which has been implementing this model since 1988, stands as a testament to its effectiveness.
Government-backed initiatives further strengthen coordinated practices. Standardized guidelines, such as those outlined in ISO/IEC 29147, help clarify the roles of everyone involved – whether it’s reporting, validating, fixing, or informing the public – making the process more predictable and efficient. However, even with these benefits, practical challenges can sometimes hinder the process.
Problems with Coordinated Disclosure
While CVD has its strengths, certain obstacles can disrupt the coordination process. One major issue is vendor unresponsiveness. When vendors lack proper systems for receiving vulnerability reports or fail to respond altogether, the entire process can grind to a halt. To address this, CISA may step in and disclose the vulnerability as early as 45 days after initial contact if the vendor doesn’t respond or fails to set a reasonable timeline for a fix.
The complexity of modern software supply chains adds another layer of difficulty. Vulnerabilities often affect components used by multiple organizations, making it challenging to coordinate an effective response across all parties involved. Different organizations may also operate at varying speeds, leading to friction when one group is ready to disclose while others are still working on a solution. The longer the embargo period, the greater the risk of leaks – whether accidental or intentional.
High-profile vulnerabilities introduce additional complications. Vendors may delay addressing other critical issues due to concerns over public perception. There’s also the possibility that someone else could independently discover the same vulnerability, resulting in an uncoordinated disclosure while the original group is still preparing a patch. As the CERT Guide to CVD aptly describes, vulnerability disclosure often feels like a "wicked problem… difficult or impossible to solve because of incomplete, contradictory, and changing requirements".
Full Disclosure: Benefits and Drawbacks
Why Full Disclosure Works
Full disclosure thrives on transparency, pushing for swift action when vulnerabilities come to light. As highlighted in the CERT Guide to CVD:
Knowledge of the existence of a vulnerability is often the key driver causing patches to be deployed.
Without public awareness, system administrators might procrastinate or entirely skip updates, leaving systems vulnerable to known exploits.
This method also prevents vendors from quietly rolling out undocumented fixes – patches that aren’t properly detailed in release notes. When updates lack clear documentation, users might underestimate their importance, leading to lower adoption rates. Public disclosure ensures vulnerabilities are taken seriously and gives users the information they need to assess how these flaws could impact their systems.
Another key advantage of full disclosure is its role in holding companies accountable. When vendors delay addressing security issues, making the details public can often be the only way to prompt action. Security expert Bruce Schneier sums it up well:
Full disclosure – the practice of making the details of security vulnerabilities public – is a damned good idea. Public scrutiny is the only reliable way to improve security, while secrecy only makes us less secure.
Once vulnerabilities are made public, they become a reputational issue that companies can’t ignore. This approach not only drives timely patching but also creates a lasting record of vulnerabilities, offering valuable insights for improving long-term security. While transparency has its advantages, it isn’t without risks.
Problems with Full Disclosure
The biggest challenge with full disclosure lies in its timing. Releasing detailed information about a vulnerability before a patch is available creates a dangerous "remediation gap." During this period, attackers have everything they need to exploit the issue, while defenders are left scrambling without a fix. The CERT Coordination Center warns:
Disclosing such information without review and mitigation only opens the public up to exploitation.
Even partial disclosure – acknowledging a vulnerability without providing full details – can be risky. Skilled attackers may still use this limited information to craft exploits. This threat is particularly alarming for critical infrastructure and systems where exploitation before a patch is ready could lead to severe real-world consequences.
Another drawback of full disclosure is the strain it can place on resources. High-profile vulnerabilities, often branded and heavily covered in the media, can force vendors to shift priorities in ways that may not align with actual risk levels. With over 228,000 vulnerabilities documented across more than 166,000 products in the CVE database, organizations must carefully prioritize their responses. Public pressure, however, doesn’t always reflect the true severity of a threat.
How Disclosure Choices Affect Researchers and Organizations
Effects on Security Researchers
The decision between coordinated and full disclosure has a profound impact on a researcher’s workflow and professional standing. Opting for coordinated disclosure means engaging in a negotiation process with vendors. Typically, this involves an acknowledgment within 24-48 hours and a disclosure window of 45-90 days. This approach helps researchers build credibility over time, as vendors are more likely to collaborate with those who have a history of responsible reporting.
But here’s the catch: this timeline often conflicts with the realities of a researcher’s career. Major conferences are a key platform for showcasing new findings, and presenting at these events can significantly advance a researcher’s reputation. This creates a tough choice: should you wait for the vendor to develop a patch, or prioritize your conference deadline? The CERT Guide to CVD highlights this dilemma:
CVD is a social process, remember? And the game is played over and over, by players who share knowledge between rounds.
Researchers who lean toward full disclosure may gain immediate visibility, but this can strain relationships with vendors. On the other hand, those who always wait for vendors to act might miss opportunities to hold companies accountable for inaction. Disclosure timeframes, therefore, are best seen as starting points for negotiation. If discussions with vendors falter, third-party mediators like CISA or CERT/CC can step in to help.
These challenges faced by researchers ripple through to organizations, influencing how they prepare and respond to security issues.
Effects on Organizations
Just as researchers navigate tight deadlines and complex negotiations, organizations must adapt their policies to handle disclosures effectively. How an organization manages vulnerability disclosures directly affects its ability to respond to security threats and shapes public perception of its security practices. The CERT Guide to CVD emphasizes this point:
The number of vulnerabilities found in a vendor’s products is less valuable as an indicator of the vendor’s security stance than the consistency of its response to vulnerabilities in a comprehensive and timely manner.
Organizations that implement a Vulnerability Disclosure Policy (VDP) set clear expectations for researchers and reduce the risk of surprise full disclosures. A robust VDP should outline which systems are in scope, provide clear contact details, and include "safe harbor" language to protect researchers acting in good faith. This proactive approach can turn potential crises into opportunities to showcase readiness.
When vendors mishandle relationships with researchers, it can create significant challenges. A lack of trust or hostile treatment often increases friction in the reporting process, which can derail the entire effort. CISA underscores the importance of timely responses: if vendors are unresponsive or fail to establish a reasonable remediation timeline, CISA may disclose vulnerabilities as early as 45 days after initial contact, even if a patch isn’t ready. Similarly, under the EU’s NIS2 Directive, Member States are required to adopt and publish CVD policies by October 17, 2024, signaling that coordinated disclosure is no longer just a recommendation – it’s becoming a regulatory standard.
Modern software systems, with their layers of complexity, add another hurdle. Vulnerabilities often involve components from multiple vendors, requiring coordination across various development timelines and patching processes. This makes the collaborative and social aspects of CVD even more critical for effective vulnerability management.
Conclusion
Navigating the complexities of vulnerability disclosure is no simple task. Keeping vulnerabilities entirely under wraps leaves users exposed if attackers independently discover them, while revealing them immediately can hand adversaries a clear path to exploitation before a fix is ready. This delicate balancing act is why the industry has leaned toward Coordinated Vulnerability Disclosure (CVD) – a method that aims to minimize harm by giving defenders time to respond while limiting opportunities for attackers. The goal is to coordinate the release of fixes and information to reduce the window of exposure. This approach highlights the importance of flexibility in disclosure practices.
Striking the right balance between transparency and security is essential, as we’ve explored. The context of each situation dictates the best course of action. For instance, if a vulnerability is already being exploited in the wild, the timeline for disclosure must accelerate, regardless of any prior plans. Adapting these methods to match the evolving threat landscape is critical. As the CERT Guide aptly points out:
The number of vulnerabilities found in a vendor’s products is less valuable as an indicator of the vendor’s security stance than the consistency of its response to vulnerabilities in a comprehensive and timely manner.
Ultimately, the most effective disclosure practices rely on good faith from all parties involved. Clear policies, open communication, and the ability to adjust based on circumstances lead to better outcomes than rigidly adhering to one extreme or another. Whether you’re a researcher or part of an organization, these principles are key to managing vulnerabilities effectively across the cybersecurity ecosystem.
FAQs
What are the main advantages of Coordinated Vulnerability Disclosure (CVD)?
Coordinated Vulnerability Disclosure (CVD) plays a key role in strengthening cybersecurity by encouraging teamwork between the individuals who discover vulnerabilities and those responsible for addressing them. The main objective is simple yet crucial: limit potential damage by giving system defenders the information they need before bad actors can exploit the issue.
At its core, CVD relies on good faith from those reporting vulnerabilities. This mutual trust promotes openness and collaboration, reducing unexpected challenges and easing tensions during what can often be a high-pressure process. By aligning the timing of vulnerability reports with their fixes, CVD contributes to building a more secure digital landscape for everyone involved.
What are the risks of Full Disclosure when no immediate patch is available?
When it comes to handling security vulnerabilities, full disclosure – where all details about a flaw are shared publicly as soon as it’s discovered – can create serious risks if a fix isn’t ready. This method essentially hands attackers the tools they need to exploit the issue, potentially causing widespread harm before a solution can be put in place.
On the other hand, coordinated vulnerability disclosure (CVD) takes a more measured approach. It involves collaborating with vendors to develop and release a fix before revealing the vulnerability to the public. This strategy minimizes the time attackers have to exploit the issue while ensuring users are protected as quickly as possible. Striking the right balance between transparency and security is crucial to addressing vulnerabilities without causing unnecessary harm.
Why is coordinated vulnerability disclosure increasingly adopted in regulatory policies?
Coordinated vulnerability disclosure (CVD) is gaining traction in regulatory frameworks because it effectively balances security needs with transparency. By fostering collaboration among researchers, organizations, and regulators, CVD ensures vulnerabilities are addressed responsibly, reducing the risk of exposing systems to unnecessary threats.
This method is increasingly preferred because it limits potential harm to both users and businesses while encouraging ethical behavior in cybersecurity. Many regulatory bodies now acknowledge its role in building trust and raising security standards across the board.

