Logistics companies handle vast amounts of sensitive information daily – addresses, payment details, and shipment data. This makes them attractive targets for cyberattacks. To safeguard this data, firms must comply with strict privacy laws, implement strong security measures, and train employees effectively. Key takeaways include:
- Regulations to Follow: Laws like GDPR (EU) and CCPA/CPRA (California) require companies to protect personal data or face hefty fines (up to €20M or $7,500 per violation).
- Access Control: Use principles like "Least Privilege" and Multi-Factor Authentication (MFA) to limit data access.
- Encryption: Protect data both in transit (e.g., TLS 1.3) and at rest (e.g., AES-256 encryption).
- Employee Training: Regular education helps prevent human errors, which contribute to 68% of breaches.
- Breach Response: Have a clear plan for detecting, containing, and notifying customers about breaches.
With rising threats and evolving laws, logistics companies must prioritize data protection to maintain customer trust and avoid costly penalties.
Cybersecurity in the Supply Chain | Protecting the Digital Backbone of Global Logistics
Know Your Data Privacy Regulations
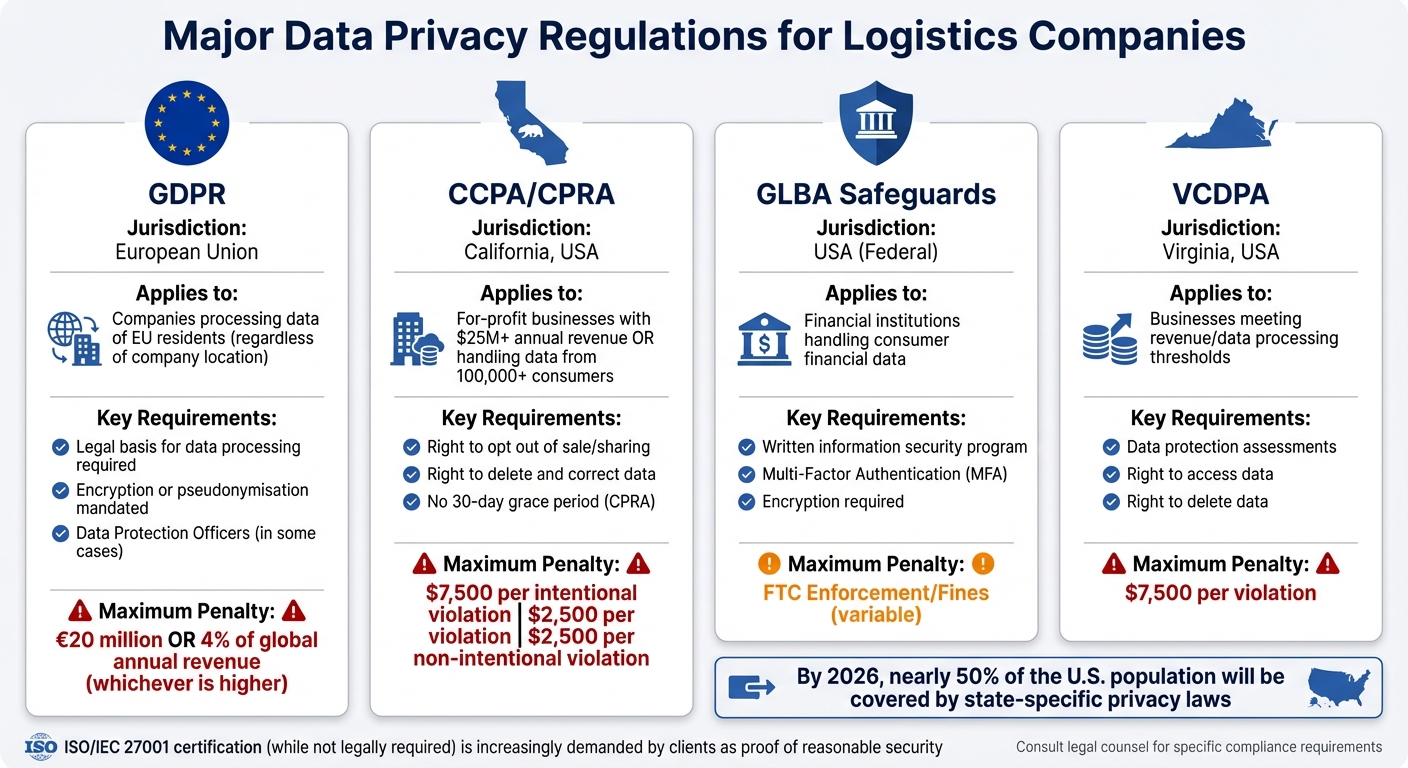
Major Data Privacy Regulations for Logistics Companies: Compliance Requirements and Penalties
Understanding and applying the right data privacy laws is essential for building a compliance program. These laws can vary significantly depending on where your customers are located, how much revenue your business generates, and the nature of the goods you handle.
Major Data Privacy Laws
The General Data Protection Regulation (GDPR) governs any logistics company processing the data of EU residents. It requires a lawful basis for data processing and mandates safeguards like "encryption or pseudonymisation." Non-compliance can result in penalties as high as €20 million or 4% of global annual revenue.
In the U.S., the California Consumer Privacy Act (CCPA) and its successor, the California Privacy Rights Act (CPRA), set the benchmark for state-level data privacy. These laws apply to for-profit businesses operating in California that meet specific criteria, such as generating over $25 million in annual revenue or handling data from more than 100,000 consumers. California residents are granted rights to delete, correct, and opt out of the sale or sharing of their personal information. Violations carry steep penalties: $7,500 per intentional breach and $2,500 for non-intentional violations. Notably, the CPRA eliminated the previous 30-day grace period for correcting violations.
By 2026, nearly half of the U.S. population is expected to fall under state-specific privacy laws, including Virginia’s VCDPA, Colorado’s CPA, Connecticut’s CTDPA, and Texas’s TDPSA. Additionally, sector-specific regulations like HIPAA, GLBA Safeguards, and the FTC Act may apply depending on the type of data being processed.
Although not a legal requirement, ISO/IEC 27001 serves as a widely recognized international standard for demonstrating "reasonable security" and compliance with various regulations. Many clients and partners now require ISO 27001 certification as a prerequisite for doing business.
| Regulation | Jurisdiction | Key Requirement | Max Penalty |
|---|---|---|---|
| GDPR | European Union | Legal basis for processing; Data Protection Officers (in some cases) | 4% of global revenue or €20M |
| CCPA/CPRA | California, USA | Right to opt out of sale/sharing; Right to delete/correct | $7,500 per intentional violation |
| GLBA Safeguards | USA (Federal) | Written information security program; MFA; Encryption | FTC Enforcement/Fines |
| VCDPA | Virginia, USA | Data protection assessments; Right to access/delete | $7,500 per violation |
Understanding these regulations is just the first step. Applying them effectively across diverse operations is where the real challenge lies.
Common Compliance Obstacles
One of the biggest hurdles is determining which laws apply to your operations. This depends heavily on your customers’ locations. For example, GDPR applies based on where your customers live, not where your servers are located. A Texas-based logistics company shipping to customers in Berlin must still comply with GDPR.
Another challenge is managing international data transfers. These occur when data is sent to or accessed from a foreign server. Some countries, like Russia, the UAE, and Saudi Arabia, have data localization laws requiring personal data to be stored on local servers.
Third-party vendor oversight is equally critical. Logistics companies often act as processors, handling data on behalf of shippers and clients (the controllers). It’s essential to have compliant Data Processing Agreements (DPAs) with all partners to clearly define data-handling responsibilities. Even when subcontracting to carriers or warehouses, your company remains accountable for ensuring compliance.
To address these challenges, start with a thorough data inventory. Identify the personal information you collect, its sources, how it’s received, and where it’s stored – whether in the cloud, on mobile devices, or in physical files. Map the flow of data within your business to understand which jurisdictions’ laws apply during transit. This step connects your understanding of regulations with actionable compliance measures. Tools like the NIST Privacy Framework can help create "Profiles" that align your privacy practices with both business goals and legal obligations.
Set Up Access Controls and Authentication
After mapping your data flows and understanding regulatory requirements, the next step is to establish strong access controls and authentication measures. Why is this so important? Because the cost of a data breach is climbing. In the U.S., the average breach cost jumped from $4.45 million in 2023 to $4.88 million in 2024. A significant portion of these costs comes from compromised credentials and excessive permissions.
"Companies that haven’t solved for access control are not only putting themselves at risk – they are also suboptimizing every dollar of their cybersecurity spend." – Richard Bird, Forbes Technology Council
The idea is simple: employees should only access the data they need to do their jobs. For example, a warehouse worker managing inventory doesn’t need access to customer payment details. Similarly, a customer service representative tracking deliveries shouldn’t control warehouse machinery. This approach, called the Principle of Least Privilege (PoLP), limits damage if an account is compromised. Once access is under control, it’s time to focus on authentication.
Multi-Factor Authentication (MFA)
MFA adds a crucial layer of security by requiring users to verify their identity using at least two of three factors:
- Something they know: A password or PIN.
- Something they have: A smartphone or physical token.
- Something they are: Biometric data like a fingerprint or facial recognition.
Even if a password is stolen, MFA makes unauthorized access far more difficult. For logistics companies, especially those with remote teams or third-party partners, MFA is critical. Combine it with tools like Virtual Private Networks (VPNs) or Zero Trust Network Access (ZTNA) to secure connections for drivers, warehouse staff, and vendor systems. Single Sign-On (SSO) is another smart addition, simplifying authentication across applications while allowing IT teams to monitor and revoke access instantly when needed.
For even greater security, consider adaptive MFA. This approach adjusts verification requirements based on risk. For instance, if an employee logs in from their usual office during work hours, a simple password and push notification might suffice. But if the login comes from an unfamiliar device or location, the system could demand extra verification or block the attempt altogether. Despite its effectiveness, Microsoft reports that only about half of Azure Active Directory global administrators currently use MFA.
Role-Based Access Control (RBAC)
While MFA strengthens individual logins, RBAC organizes permissions at a broader level. Instead of assigning access rights to each employee manually, RBAC groups users based on their job functions and grants permissions accordingly. For instance, roles like "Inventory Management" or "Shipment Tracking" can be created based on operational needs rather than specific job titles. This makes scaling access management much easier as your business grows.
To streamline this further, use role hierarchies. A Senior Logistics Manager, for example, can inherit all the permissions of a Logistics Coordinator, plus additional administrative rights. Avoid creating global "Admin" roles; instead, assign scoped roles that limit administrative access to specific departments or regions.
Another essential practice is Separation of Duties (SoD). This ensures no single person has control over an entire process. For example, the employee creating a purchase order shouldn’t be the one approving it. Integrating RBAC with HR systems also helps by automating access for new hires and revoking it immediately when employees leave. Regular audits are key to identifying "permission drift", where employees accumulate unnecessary access over time.
| Logistics Role | Permitted Actions | Sensitive Data |
|---|---|---|
| Logistics Manager | View shipment schedules, update routes, monitor inventory levels | Financial records, customer payment details |
| Warehouse Worker | Log incoming stock, update bin locations, view pick lists | Shipment pricing, contract terms with carriers |
| Procurement Manager | Create purchase orders, manage vendor contracts | Driver behavioral data, vehicle maintenance logs |
| Customer Service | Track shipment status, view delivery addresses | Warehouse machinery controls, payroll data |
For urgent situations, consider "break-glass" roles. These temporary roles grant elevated access for emergencies without the need to create permanent, overly privileged accounts.
Encrypt Data During Storage and Transmission
Once access controls are in place, encryption becomes the next line of defense to secure data throughout its lifecycle. Encryption works by converting sensitive information into unreadable ciphertext, which can only be deciphered with a specific key. Without this key, any stolen data is essentially useless to attackers. As Emrick Etheridge, an Information Security Expert at DataGuard, explains:
Encrypted data is worthless to unauthorized parties without the decryption key.
The challenge lies in protecting data in two key states: in transit (when it’s moving across networks) and at rest (when it’s stored in databases or devices). While the methods differ, the goal stays the same – encryption significantly reduces the damage of potential breaches.
Encryption for Data in Transit
Data in transit includes any information being sent over the internet or internal networks, such as customer order details or shipment updates. To secure these communications, Transport Layer Security (TLS) is the go-to standard. TLS creates an encrypted channel between the user and the server, often signaled by the HTTPS padlock in your browser’s address bar. For the best protection, opt for TLS 1.3, which offers faster connections and stronger encryption compared to older versions.
For network-to-network communications, like those between warehouse systems and cloud infrastructure, use IPsec-encrypted VPNs. For example, AWS encrypts data traveling between its regions at the physical layer before it ever leaves secure facilities. Beyond that:
- Use TLS 1.3 for securing web communications.
- Implement S/MIME or PGP for encrypting emails.
- Rely on SSH for managing remote systems.
These measures ensure that data remains secure while in transit, but stored data requires just as much attention.
Encryption for Data at Rest
Data stored in databases, hard drives, or cloud environments needs a robust encryption plan. The gold standard here is AES-256 (Advanced Encryption Standard with 256-bit keys), which is widely supported by cloud platforms. For instance:
- Azure Storage Service Encryption, AWS S3 server-side encryption, and Google Cloud‘s default encryption all use AES-256 without requiring custom cryptographic tools.
For logistics databases containing sensitive information like customer details or shipment records, enable Transparent Data Encryption (TDE). TDE encrypts data at the page level, safeguarding physical database files. Additionally:
- Configure cloud environments to automatically encrypt all new storage volumes, database instances, and snapshots.
- Ensure that backups are encrypted to the same standard as the primary data.
Field devices like driver laptops and mobile scanners also need protection. Tools like BitLocker (for Windows) or LUKS (for Linux) provide full disk encryption (FDE), which ensures that even if a device is lost or stolen, its data remains secure. However, encryption is only as reliable as its key management. To strengthen this:
- Store encryption keys in a Key Management System (KMS) or Hardware Security Module (HSM).
- Automate key rotation to reduce the risk of key compromise.
- Set up alerts for key deletion to avoid permanent data loss.
Recommended Encryption Tools for Logistics
| Encryption Type | Best Use Case in Logistics | Recommended Technology |
|---|---|---|
| Full Disk (FDE) | Laptops, mobile scanners, and field devices | BitLocker, LUKS |
| Database (TDE) | Customer databases and shipment records | Azure SQL TDE, AWS RDS |
| Object Storage | Digital bills of lading and document images | AWS S3, Azure Blob Storage |
| Removable Media | Offline backups and data transfers | Drive encryption (BitLocker To Go) |
sbb-itb-760dc80
Train Employees on Data Privacy
Even the strongest encryption and access controls can falter if employees unknowingly expose sensitive information. According to Verizon‘s 2024 Data Breach Investigations Report, 68% of all data breaches involve the "human element," which includes unintentional mistakes by employees. This is particularly concerning in logistics, where staff regularly handle shipment manifests, customer addresses, and payment details. A single click on a phishing email could potentially compromise thousands of records. The Federal Trade Commission puts it plainly:
"A well-trained workforce is the best defense against identity theft and data breaches." – Federal Trade Commission
To combat these risks, annual refresher courses help employees stay vigilant against emerging threats. Beyond that, regular communication fosters a workplace culture that prioritizes security. For employees with elevated access – like database administrators, HR personnel, or shipment coordinators – role-specific training is crucial. These sessions should address advanced topics, such as embedding privacy clauses in vendor contracts or limiting access to shared drives. This tailored approach is especially important for defending against social engineering attacks.
Training on Social Engineering and Phishing
Logistics companies are frequent targets of spear phishing, where attackers pose as executives or trusted partners to manipulate employees. Past breaches caused by reused passwords highlight the urgency of teaching staff to identify warning signs, including urgent messages (e.g., "Your account will be suspended!"), mismatched sender domains, and requests for sensitive information.
Employees should be trained to verify suspicious requests using independently sourced contact information rather than replying directly. They should also learn how to hover over links (or press-and-hold on mobile devices) to reveal their true destinations. To gauge employee preparedness, companies can run phishing simulations using free tools like those offered by Microsoft or KnowBe4. Immediate feedback for those who fall for these tests can help reinforce lessons. In some cases, restricting network access for employees who fail to complete required training may be necessary. This proactive training complements technical safeguards, creating a more comprehensive approach to data privacy.
Safe Data Handling Procedures
Awareness of phishing is just one piece of the puzzle – proper data handling practices are equally critical. Employees should follow clear protocols to manage sensitive data throughout its lifecycle. Physical security is a must: sensitive documents should never be left unattended on desks, and file cabinets should always be locked at the end of a shift. For remote workers, laptops should be kept out of sight in vehicles or public spaces, and all remote access should be secured with encryption.
When transmitting sensitive data, employees should encrypt files before sending them over public networks and use secure protocols like Transport Layer Security (TLS). For disposal, paper records should be cross-shredded, while IT teams must use "wipe" programs to securely erase data from old hard drives – including those in digital copiers, which should be wiped monthly. Employees should also be encouraged to report lost devices or unusual network activity immediately to the Privacy Office or IT department.
These practices, combined with regular training, build a strong foundation for safeguarding sensitive information.
Create Data Breach Response Procedures
Even the strongest defenses can falter. The global average cost of a data breach is a staggering $4.44 million per incident, and breaches often go unnoticed for months. For logistics companies managing thousands of customer addresses, shipment details, and payment information daily, such delays can lead to severe fallout. As the Office of the Australian Information Commissioner (OAIC) emphasizes:
"A quick response to a data breach, based on an up-to-date data breach response plan, is critical to effectively managing a breach."
A well-documented response plan is essential, outlining specific actions for every team member. This plan should establish clear escalation criteria – such as the number of affected individuals or the severity of the risk – that trigger the activation of a dedicated response team. This team may include a leader, project manager, privacy officer, legal experts, IT/forensics specialists, and communications professionals. Regular testing through simulated breach scenarios ensures the team is prepared when it counts.
Build a Data Breach Response Plan
Your response team needs the tools and authority to act immediately. The response plan should detail initial containment steps to stop the breach from spreading. For instance, delays in responding to ransomware attacks have previously allowed them to cripple entire departments. The plan must also include protocols for assessing the impact on affected individuals and identifying exactly what data was compromised, whether it’s shipping records, customer addresses, or payment details.
It’s critical to understand that while data integrity can often be restored from backups, breaches of confidentiality are permanent. As NIST explains:
"Once digital data is in the hands of an unauthorized user, there is no guaranteed method by which to get all copies of the data back." – NIST SP 1800-29
Recovery efforts should include offering credit monitoring to affected customers and implementing stronger security measures to prevent future incidents. Keep an up-to-date contact list for all response team members and their backups, and, if applicable, incorporate any external resources provided by your cyber insurance policy.
These proactive steps ensure that once a breach is detected, your team can quickly move into action, focusing on containment, notification, and remediation.
Notify Customers and Regulators
Once the breach is contained, it’s vital to notify all affected individuals promptly. These notifications should clearly explain the scope and severity of the breach, enabling recipients to take protective actions. Depending on the type of data compromised, you may also need to notify the Federal Trade Commission under the FTC Safeguards Rule (effective May 2024). For large-scale breaches or those involving sensitive health data, media notifications may also be required.
Having pre-drafted templates and clear timelines in place can streamline the notification process and ensure compliance with legal obligations. Your communication strategy should outline which external parties – such as regulators, law enforcement, or the media – need to be informed. After the incident, conduct a thorough review to identify the root cause of the breach and evaluate the effectiveness of your response. Address any weaknesses uncovered during this review. As the OAIC notes:
"An effective data breach response can support consumer and public confidence in an entity’s respect for individual privacy, and the entity’s ability to manage personal information in accordance with community expectations."
This transparency not only helps rebuild trust but also demonstrates your commitment to safeguarding customer data.
Conclusion
Protecting data privacy in logistics is an ongoing effort that requires consistent attention and action. From robust encryption methods to comprehensive employee training, every measure plays a role in building a dependable privacy strategy. The digital threat landscape is constantly shifting – cybersecurity roles have increased by over 300,000 since 2016, showcasing the growing need for vigilant security management. New technologies and operational adjustments often introduce fresh data flows, each requiring updated safeguards. As the Information Commissioner’s Office emphasizes, "Clear accountability for security will ensure that you do not overlook these issues, and that your overall security posture does not become flawed or out of date".
Regulatory frameworks are evolving just as rapidly. For instance, the NIST Privacy Framework is designed to adapt to advancements like artificial intelligence and the Internet of Things. Similarly, the UK GDPR mandates organizations to "routinely test and evaluate" their security measures. This makes regular audits, updated training programs, and penetration testing essential – not optional. These frameworks highlight the importance of staying proactive and flexible in security practices.
The consequences of neglecting data privacy are severe. Research shows that 87% of customers would immediately stop doing business with a company if they had doubts about its data protection measures. Beyond financial penalties, a breach of confidentiality is irreversible – unlike a system crash that can be solved with backups, leaked data cannot always be fully recovered.
To keep up with evolving regulations and threats, businesses must foster a strong internal security culture. This includes monitoring outgoing network traffic for anomalies, replacing default vendor passwords promptly, and implementing a 3-2-1 backup strategy (three copies of data, stored on two devices, with one kept off-site). Regular refresher training ensures employees are prepared to counter emerging threats like AI-driven phishing and social engineering. Companies that prioritize these ongoing improvements often experience a 2% to 7% boost in sales revenue.
Your customers entrust you with sensitive information like addresses, payment details, and shipment data. Uphold that trust by embedding privacy into every aspect of your operations.
FAQs
What data privacy regulations should logistics companies follow?
Logistics companies across the United States are required to follow important data privacy regulations aimed at safeguarding customer information. Key regulations include the Gramm-Leach-Bliley Act, the Data Privacy Framework, and the Safeguards Rule. These laws mandate measures such as encryption, strict access controls, and routine risk assessments to protect sensitive data.
By adhering to these rules, companies can better secure private information and minimize the chances of data breaches. Additionally, investing in employee training and keeping up with changes in regulations are critical for maintaining strong data privacy practices.
What steps can logistics companies take to train employees and prevent data breaches?
Logistics companies can take proactive steps to avoid data breaches by offering employees regular cybersecurity training. This training should cover key areas like spotting potential threats, practicing safe data handling, and identifying unusual or suspicious activities. Using scenario-based learning and real-world examples can make the sessions more engaging and relatable for employees.
It’s also crucial to educate employees about their individual responsibilities when it comes to safeguarding sensitive information. This includes understanding the importance of access controls and using secure methods for communication. By building a workplace culture that prioritizes security awareness, companies can lower the chances of breaches and ensure their teams are ready to tackle evolving cyber risks.
What are the best ways to encrypt data in logistics operations?
Protecting sensitive information is a top priority in logistics, and encryption plays a key role in keeping data secure. There are two main types to focus on: encryption at rest, which safeguards stored data, and encryption in transit, which protects data as it moves through networks. Both are critical for preventing unauthorized access.
To strengthen security, it’s important to use advanced encryption algorithms and carefully manage encryption keys. Additionally, classify your data based on its sensitivity – this allows you to apply the highest level of encryption to your most critical information. Regularly updating encryption protocols and adhering to industry standards ensures you’re prepared to counter new security threats. These steps not only protect your data but also help maintain customer trust and meet regulatory obligations.

