Want to handle cyberattacks effectively? The key lies in incident response training. Here’s what you need to know:
- Why It Matters: Quick responses reduce downtime and costs. Without training, stress and mistakes can turn manageable threats into disasters.
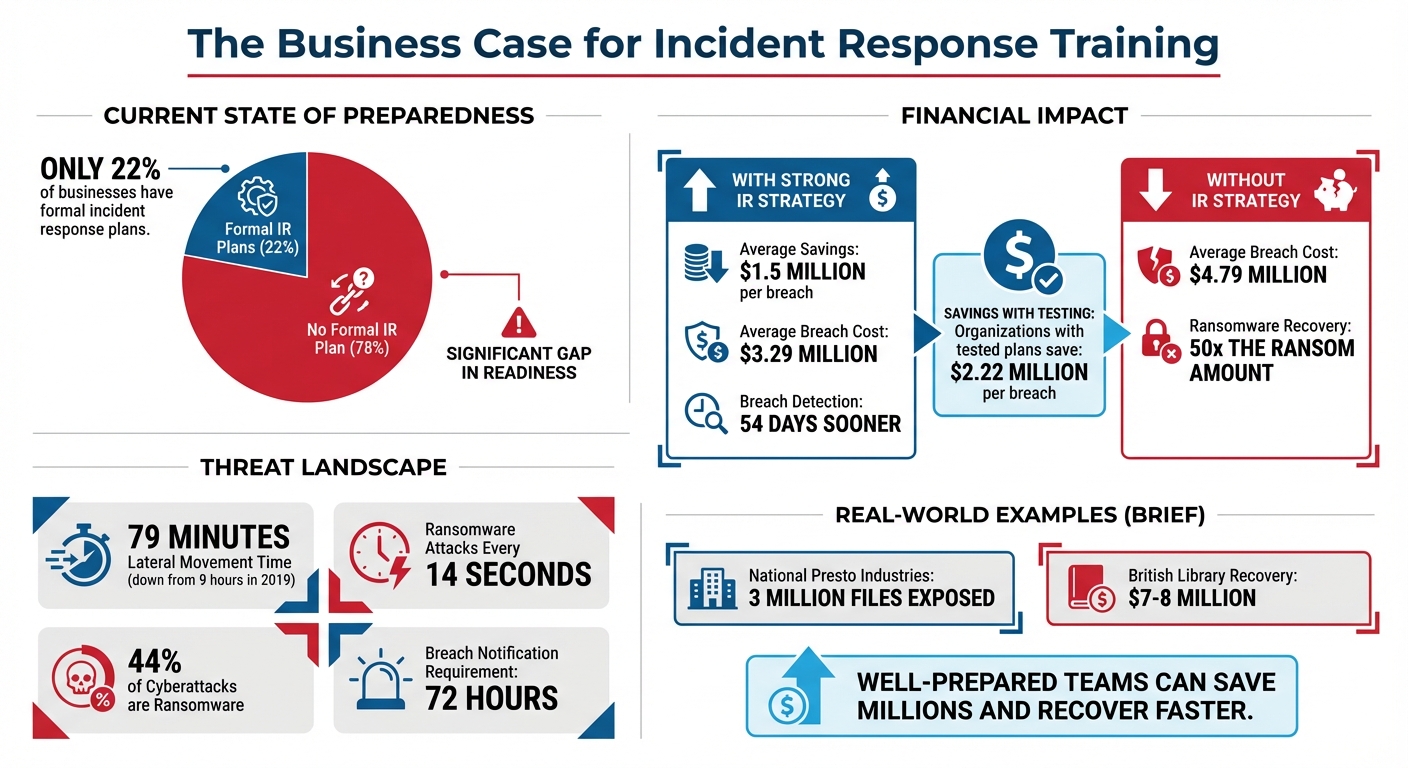
- Challenges: Only 22% of businesses have formal plans. Many fail due to time constraints, poor coordination, and outdated methods.
- Key Steps:
- Define clear roles to avoid confusion during crises.
- Use realistic simulations, not just theoretical exercises.
- Set up secure communication channels for accurate updates.
- Regularly test and update your response plan.
Bottom line: A well-prepared team can save millions and recover faster. Start by focusing on clarity, practice, and communication.
Incident Response Training Statistics and Cost Savings
Defining Roles and Responsibilities
Problems Caused by Unclear Roles
When a cyberattack occurs and no one knows who’s in charge, things can spiral out of control quickly. Without clearly assigned roles, teams may duplicate efforts or, worse, miss critical steps entirely. Even a brief delay in response can lead to massive financial losses and reputational harm. Take the case of National Presto Industries in September 2025: an InterLock ransomware attack exposed nearly three million files. The lack of clear authority slowed their recovery and caused significant damage to their public image.
"Having a well-prepared incident response team, with clear roles, responsibilities, and authority, is often what separates a fast recovery from long-term damage."
– Sygnia Team
The numbers speak for themselves. Companies with strong incident response strategies save an average of $1.5 million per breach. On the flip side, recovering from a ransomware attack can cost up to 50 times more than the ransom itself. To avoid these pitfalls, organizations need a structured framework that defines who does what during a crisis.
Creating a Clear Role Framework
One way to establish this structure is by adopting widely recognized standards like NIST SP 800-61. This "Computer Security Incident Handling Guide" provides a solid foundation for assigning roles and organizing response processes. Reviewing this framework annually and getting buy-in from senior leadership ensures it stays relevant and effective .
A well-rounded incident response team includes both technical and non-technical roles. On the technical side, you might have an Incident Commander, Technical Lead, and Security Analysts. Non-technical roles could include a Communications Lead, Legal Counsel, and HR Representative. These roles should align with existing job titles to streamline integration .
The importance of such a framework was highlighted in October 2023 when the British Library faced a ransomware attack. Recovery costs ballooned to $7–$8 million as their restoration efforts dragged on.
Another critical element is secure communication. Before a crisis strikes, establish out-of-band communication channels – like encrypted messaging apps – that remain operational if primary corporate networks are compromised. Assign specific contacts to handle key responsibilities, such as the CEO or Corporate Communications Lead for media relations and the CISO or Legal Counsel for government interactions .
"Security incidents lead to panic and confusion… Keeping calm and focused on what matters requires everyone to have a clearly defined role and specific responsibilities within a standardized process."
– Joshua Selvidge, CTO, PurpleSec
Training & Drills: Incident Response Team Prep Guide
Using Realistic Training Scenarios
By building on well-defined roles, realistic scenarios help teams sharpen their coordination and decision-making skills, ensuring they’re better prepared to handle real incidents.
Why Theoretical Training Falls Short
Passive training methods – like watching videos or reviewing policies – don’t prepare teams for the chaos of an actual crisis. While these approaches may teach employees to avoid risky behaviors, they don’t equip them to work together, make quick decisions, or regain control during an active breach. Unlike theoretical exercises that focus on compliance, realistic scenarios push teams to think on their feet under pressure.
When incidents occur, relying solely on written procedures often leads to costly mistakes. For instance, a team member might delete a suspicious file in an attempt to stop the issue, unknowingly destroying crucial forensic evidence needed to trace the attack’s source. Miscommunication during these moments can make things worse, exposing flaws like unclear responsibilities, outdated documentation, or poorly configured tools. Organizations with thoroughly tested incident response plans save an average of $2.22 million per breach compared to those without.
"The best time to prepare for an incident is before it happens… it needs to be part of how your organization operates: tailored to specific roles, aligned with your cyber readiness strategy, and backed by regular practice, not just theory."
– Sygnia Team
Given these shortcomings in theoretical training, hands-on exercises are essential.
How to Implement Realistic Training
Craft training scenarios that reflect your organization’s actual risks. For example, a small e-commerce business should focus on simulations involving ransomware or payment card breaches, rather than overly complex threats that are unlikely to occur. Realism is critical – if scenarios feel disconnected from reality, participants may lose interest, and the exercise won’t yield valuable insights.
Incorporate unexpected challenges to mimic real-world conditions. For instance, you could simulate a situation where the only person with access to vital backups is unreachable, or where a journalist demands an immediate statement. These curveballs force teams to adapt quickly and highlight weaknesses in redundancy planning.
"Ok, Jenny, the only person who has access to that information is on vacation at a resort with no cell service and no email, now what are you going to do?"
– Karen Sprenger, Managing Partner for Technology, LMG Security
Create Emergency Action Cards – quick-reference tools containing critical information to guide decision-making under pressure. These cards eliminate the need to dig through lengthy manuals when time is of the essence. Similarly, marketing and PR teams should maintain "break glass" kits with pre-written templates for social media updates, customer communications, and shareholder notifications.
Regular drills build confidence and calmness under pressure. Update your scenarios at least once a year or whenever your IT systems evolve. Include emerging threats, like deepfakes or supply chain attacks, to keep your training relevant. After each drill, conduct a post-exercise review to analyze what went well, identify areas for improvement, and adjust your incident response plan accordingly. These exercises not only test your team’s readiness but also drive continuous improvement, ensuring your organization is prepared for the unexpected.
Improving Communication Protocols
After conducting realistic drills, ensuring rapid and clear communication becomes essential during an incident. Poor communication can escalate a manageable situation into a full-blown crisis.
Common Communication Breakdowns
The first hour of a cyber incident is often chaotic. As the Sygnia Team aptly describes:
"In the first hour of a cyber incident, information moves faster than certainty".
During this critical window, alerts flood in, and responders scramble to verify facts. Without predefined communication channels, teams risk duplicating efforts, often investigating the same issue due to uncoordinated, ad hoc communication.
Conflicting information can quickly erode trust. For instance, when multiple versions of the same incident report circulate, confusion and blind spots emerge. Internal staff might even learn about a breach from the media rather than leadership, or external statements might contradict verified technical findings. As Paul Lee, Jerzy "Yuri" Kramarz, and Martin Lee from Cisco Talos explain:
"A lack of a formal process means that everyone is doing whatever actions they believe are best in the given scenario and not necessary actions that are justified".
The financial impact of these breakdowns is stark. Organizations with well-developed incident response plans face an average data breach cost of $3.29 million, compared to $4.79 million for those without one. Muhammad Waleed, a Cyber Security Expert at Wyrdex, emphasizes:
"The way your company communicates during a cyber attack will define how your brand is remembered".
These challenges highlight the importance of having a structured, unified communication system.
Building Better Communication Systems
To address these pitfalls, it’s crucial to implement robust communication protocols. Start by establishing a "single source of truth" – a dedicated Incident Command Channel where all validated updates originate. This helps prevent the spread of rumors and unverified claims across your organization. Use a tiered communication approach: provide detailed updates to the SOC, concise summaries to department heads, and high-level overviews to executives.
Prepare pre-approved templates for SITREPs (Situation Reports), regulatory notifications, and customer statements. Having these ready to deploy saves valuable time when every second counts . Set up secure, ongoing bridge calls to ensure technical leads, legal teams, and communications staff can share verified information in real time.
Document key messages and decisions for traceability and compliance. Designate a single spokesperson – typically your CEO or CISO – to deliver external communications. This avoids the risk of technical jargon or speculation reaching the public. Above all, prioritize internal notifications. Employees should hear about a breach from leadership, not from external sources like the media.
sbb-itb-760dc80
Maintaining Current Skills
Staying on top of current skills is just as important as clear communication when it comes to tackling new and evolving threats.
Building on realistic scenarios and effective communication strategies, keeping skills sharp is the next key step in ensuring a strong incident response.
Preventing Outdated Skills
Here’s a startling shift: attackers now move laterally within systems in just 79 minutes, a dramatic change from 9 hours back in 2019. On top of that, ransomware attacks are expected to strike a new target every 14 seconds. As cyber threats grow more advanced, relying on outdated tools or methods puts your team at a huge disadvantage. With the rise of cloud-based systems, AI-driven attacks, and increasingly complex ransomware, continuous education and training aren’t optional – they’re necessary. Regular testing and thorough post-incident reviews can turn every breach into a learning opportunity. As the Cybersecurity and Infrastructure Security Agency (CISA) puts it:
"The best offense is a good defense".
Training Resources and Programs
Investing in training doesn’t have to break the bank. CISA provides free incident response training for government employees, contractors, critical infrastructure partners, and even the general public. Their tiered offerings include one-hour awareness webinars and more intensive four-hour Cyber Range training sessions. For those looking to build foundational skills, the Federal Cyber Defense Skilling Academy offers a 12-week program tailored for Cyber Defense Analysts. This program is available through the CISA Learning platform (formerly known as FedVTE).
Organizations can also take advantage of CISA’s Tabletop Exercise Packages (CTEP), which allow teams to run internal drills and uncover vulnerabilities in a safe, controlled environment. These free resources provide a straightforward way to keep your team’s skills sharp and ready to handle the fast-evolving landscape of cyber threats.
Testing Plans and Cross-Department Coordination
Once roles are defined and communication protocols are in place, the next step is regular testing to ensure your incident response plan works seamlessly. Even the most well-crafted plans remain theoretical without putting them to the test. Regular exercises are critical for ensuring your team can respond quickly and effectively during a breach. Without these drills, things like tool integration, role clarity, and decision-making under pressure remain unproven.
Why Testing Your Plans Matters
Testing uncovers hidden weaknesses in your processes, leadership structure, and technical tools. It also forces teams to establish clear decision-making authority – such as who has the power to shut down systems or contact law enforcement – long before an incident occurs.
The urgency to test is backed by numbers. Ransomware accounts for 44% of cyberattacks, and many privacy laws mandate breach notifications within just 72 hours. Testing also ensures that tools like EDR (Endpoint Detection and Response) and SIEM (Security Information and Event Management) are properly integrated and that your response plan evolves with new threats and infrastructure updates. Organizations should aim to conduct tabletop exercises annually – or even every three to six months for new teams or after significant changes.
Effective testing isn’t just about IT. It requires collaboration across multiple departments.
Working Across Departments
Incident response is not solely an IT responsibility. Successful testing involves teams from Legal, HR, PR, and executive leadership. Assigning a Communications Liaison ensures that messaging to executives and external stakeholders is handled smoothly, allowing technical teams to focus on containment. Shared playbooks can streamline risk assessments and ensure everyone is on the same page.
Additionally, establish out-of-band communication channels to maintain connectivity if primary systems are compromised. After each exercise, conduct a quick debrief (commonly called a "hotwash") and document lessons learned in an After-Action Report.
With cross-department collaboration in place, the next step is choosing the right testing method.
Tabletop Exercises vs. Live Drills
Different testing approaches serve different purposes. Here’s a closer look at how they compare:
| Exercise Type | Method | Advantages | Disadvantages | Best Use Case |
|---|---|---|---|---|
| Tabletop Exercise | A discussion-based walkthrough of a hypothetical scenario. | Low cost; safe environment; highlights gaps in roles and decisions. | Theoretical; doesn’t test technical tools or real-time pressure. | Ideal for new teams, testing policies, or engaging the board. |
| Live Drills / Simulations | Immersive, real-time simulations with little to no notice. | Tests processes under pressure; validates tool integration. | Resource-heavy; risk of disrupting business operations. | Best for mature teams and testing speed and containment efforts. |
As Adam Harrison, Managing Director at FTI Consulting, puts it:
"Tabletop exercises can expose blind spots and help response teams build the muscle memory needed to act fast when the real thing hits".
Start with tabletop exercises to address communication and decision-making gaps. Once your team is comfortable, move on to live drills to test their readiness under real-world pressure.
Conclusion
Creating a prepared incident response team isn’t a one-and-done task – it’s an ongoing process of refining strategies and staying ready for anything. The key elements? Clear roles, realistic training, effective communication, and regular testing. When everyone knows their responsibilities, training mirrors real-world challenges, communication flows seamlessly, and testing uncovers weak spots, your team is set up to handle incidents effectively.
Here’s why it matters: well-tested response plans can save businesses an average of $2.22 million per breach and help teams detect breaches 54 days sooner. Yet surprisingly, only 22% of companies have a formal plan in place . This gap highlights just how crucial thorough preparation is.
As the Sygnia Team wisely states:
"The best time to prepare for an incident is before it happens, and that’s exactly what a well-designed response program helps you do".
This advice stresses the importance of being proactive in every aspect of incident response.
Start by assigning clear roles and responsibilities. Then, conduct realistic simulations to test decision-making under pressure. Set up secure, out-of-band communication channels, and involve key teams beyond IT – think Legal, HR, and PR – to ensure everyone is on the same page. Finally, after every exercise or incident, hold a debrief to identify lessons learned and update your plan accordingly . This thorough approach doesn’t just prepare your team on paper – it ensures they’re ready to act when it counts.
FAQs
Why are realistic training scenarios important for incident response teams?
Realistic training scenarios play a key role in equipping incident response teams to tackle real-world challenges with confidence. These exercises reveal gaps in current processes, sharpen decision-making under pressure, and encourage stronger communication and teamwork.
By replicating real incidents in a controlled setting, teams can rehearse their responses, boosting both their confidence and efficiency. This hands-on approach ensures that team members are not just technically capable but also ready to manage the intricate demands of today’s cybersecurity landscape.
What are the best practices for effective communication during a cyber incident?
To navigate a cyber incident effectively, having clear protocols and a well-thought-out communication plan in place beforehand is crucial. One smart move is to prepare pre-approved statements ahead of time. This step can help minimize confusion and reduce the risk of spreading misinformation during high-stress moments.
Stick to simple, non-technical language so that everyone involved – whether they’re customers, employees, or regulators – can easily grasp what’s happening. Before releasing any updates to the public, ensure leadership and technical teams are on the same page. This unified approach helps maintain both credibility and trust.
Equally important is providing timely and transparent updates as the situation unfolds. A steady, consistent communication strategy can safeguard your organization’s reputation, help rebuild trust, and prevent unnecessary panic or speculation.
Why is it essential to regularly test and update your incident response plan?
Keeping your incident response plan up-to-date and testing it regularly is crucial for ensuring your team can handle real-world challenges. These efforts help uncover weaknesses, confirm that roles and procedures work as intended, and adjust to emerging or changing threats. Even the best plans can become obsolete over time if they’re not revisited, potentially leaving your organization exposed.
Taking a proactive approach minimizes the chances of small issues spiraling into major crises. It also safeguards sensitive information and supports smooth operations. Regular reviews not only strengthen your team’s preparedness but also boost their confidence in managing unforeseen events with efficiency.

