Are you familiar with the nature of cybercrimes? It would be impossible to protect yourself against cyber threats that you hardly understand. You must be well aware of the risks to tackle it strategically.
While some cyberattacks can be harmless or perhaps cause a little damage, others can result in significant repercussions. An attack compromises the privacy, reliability, or the data stored in your digital system, website, or digital device.
Cybercriminals can initiate attacks to:
- Use a computer without authorization
- Access secure and personal information on people and businesses
- Hack websites for unsolicited purposes
- Install malware and viruses
- Deny services
- Access a system, digital network, or its data without authorization
Types of Cyber Threats
1. Social engineering and phishing attacks
Emails sent in phishing attacks usually appears to be coming from a trusted and reputable source like the bank or a government agency. The cyber attacker knows too well that you wouldn’t hesitate to give your personal information to an institution you trust. Additionally, the criminal will create a sense of urgency so that the victim can act fast without thinking. For instance, they could tell you that there was a criminal attempt on your account, and they need some information to safeguard it. So, you’ll probably be concerned and send the details to salvage the “situation.”

With your private details at hand, the cyber attacker will use it for their benefit. They can use your password to access your systems and spread malware or use your sensitive information to obtain credit in your name. The criminal can also access your bank accounts and steal your money.
In spear phishing, a social engineer takes some time to study their victim so that they can launch a more focused attack. For example, the attacker could research online and find your best friend’s email address. After that, they will create a similar email address and instruct you to download an attached file. If you act in a hurry and forget to pay attention to the fine details, you will download the attachment and introduce malware to your device.
Prevention
- Check the email header “Return-Path” and “Reply-to” to find out if it matches that of a trusted source
- Hover over the links to see if it goes to the URL it says it will
- Train your staff on password security and the right protocols
2. Password attacks and credential reuse
Cyber attackers have an array of techniques that they use to hack passwords. They usually begin with common ‘weak’ passwords like ‘password’ or ‘123456’. If that fails, the hackers will proceed to use the sophisticated ‘Rainbow table’ that utilizes previously cracked passwords.

Once a cyber attacker has cracked your password, they gain access to your private information. Additionally, they can request a password reset for your other accounts and prevent you from accessing them. After that, stealing your identity will be less challenging, and the cybercriminal can enjoy all the privileges of being you.
Prevention
- Ensure that none of your employees are using default passwords in their accounts
- Formulate and implement an account lockout policy in your organization, which locks accounts after a few wrong password attempts
- Discourage your staff from reusing passwords in their various accounts
- Use password managers to simplify password management
- Encourage your team to use robust and unique passwords at all times; to make it hard to crack
- Train and educate everyone about the techniques used in phishing attacks
3. Denial-of-service attacks
These attacks flood your web servers with endless requests, which makes it impossible for anyone to connect to it. And the consequences can be devastating for any business because your website experiences a prolonged downtime. You may have to deal with data loss, a damaged reputation, disappointed customers, and payouts in compensation. Common DoS and DDoS attacks include botnets, ping-of-death, TCP SYN flood attack, smurf attack, and teardrop attack.
Prevention
- Test your IT infrastructure regularly
- Have an “always-on” DoS protection
- Have protocol that helps minimize or prevent an attack
- Use more than ISP and firewall protection because cyberattacks today are a heavy load
- Adopt these options for adequate DoS protection:
- a solution that combines cloud DoS and on-prem protection
- counteraction scrub, reroute, absorb, and deflect
- protection to detect, filter, identify and protect the network
4. Man-in-the-middle (MitM) attack
In this attack, the hackers insert themselves between the private conversations of two legitimate hosts. The criminals will not only eavesdrop, but they will also disguise themselves as one or both of the parties. And they can go beyond just listening and intercepting the messages between the servers and the clients; the hackers can plant requests and edit the messages. Notably, man-in-the-middle attacks are challenging to detect. However, you can prevent them with the right security measures.
Entry points
– Malware
The hacker can invade your private conversation through software. Notably, the malware will be installed into your system when you open an attachment or download a file from an unknown source. After that, they will use malicious software to process all the information required for the man-in-the-middle attack.
– Unsecured public Wi-Fi
The hacker can insert themselves between the network and your device and take control of your private chats. So, you’ll be passing all your conversations through the invader unknowingly.
Prevention
- Add layers of protection to your confidential networks like your office Wi-Fi by setting up a VPN
- Invest in an Intrusion Detection System (IDS)
- Enhance security and user trust in your website using SSL certificates like HTTPS
5. Structured Query Language (SQL) injections
The attack can happen when a cyber attacker inserts malicious code into the SQL database. And they can achieve this by simply submitting the code into the search box of the company’s website. Additionally, the code can delete, modify, and read data once it is unleashed in the database. In some cases, a SQL injection can issue commands to the operating system or shut down your database.
Prevention
- Always validate SQL data inputs against a whitelist
- Exclude dynamic SQL and stick to stored procedures and prepared statements like parameterized queries
- Consider a least-privilege permissions model in your database
6. Zero-day exploit
Say, you have discovered a security risk in software. The best thing to do is to probably alert the company so that they can develop a patch to fix the problem. However, most people would go online to share what they have discovered and warn other users.
Cybercriminals are always on the lookout for such vulnerabilities and will take advantage of the information shared by a well-meaning user. Therefore, they will attempt to exploit it before the software developers to fix the issue.
Notably, cyber attackers prize these vulnerabilities so high. Additionally, zero-day attacks only exist after it has happened. Thus, it is not easy to defend oneself against them.
Prevention
- Don’t visit websites that lack the SSL certificate
- Secure your Wi-Fi system to protect your systems against wireless malware attacks
- Protect transmitted data by using virtual LAN, and utilizing its firewall
- Make sure that your application software and operating systems are up to date
7. Cross-site scripting (XSS)
A hacker attacks users by injecting a malicious script on a trusted website. It will require you to visit another infected web page, where you will be exposed to unpleasant scenarios. The hacker may gain access to your log keystrokes, microphones, webcams, or even remote access to your computer.
Prevention
- Run an XXS vulnerability tests
- Sanitize user data input using an HTTP request
- Educate your users on basic phishing techniques
8. Drive-by-downloads
This type of cyberattack can infect your computer without downloading anything or opening any email attachment. Instead, it thrives in the vulnerabilities in your apps, web browsers, and operating system. For instance, if you lack security updates, your device can be infected when you view a website, a pop-up, or an email.
Prevention
- Don’t keep programs and apps you do not need; more plug-ins can mean more weak spots
- Only visit sites that you trust
- Make sure that your browsers and OS have the latest updates
9. Malware
Malware is developed in the form of active content, executable codes, and scripts. The goal is to intentionally disrupt and damage computer networks, clients, servers, and computers. Common examples of malware include scareware, spyware, adware, Trojan horses, ransomware, viruses, and computer worms.
Damages caused by malware
- Damage to particular hardware components of the system, making it inoperable
- Theft of valuable information in the system
- Installation of harmful software
- Blocked access to critical components of the network
10. Insider threats
Most businesses focus on defending their systems against an external attack. However, an authorized individual within the organization can also perform a cyberattack. Notably, they have the edge over external attackers because they are familiar with the network architecture and the system’s policies. Additionally, they have authorized access, and there are fewer security measures against them.

The insider threat can crash the system by overloading the computers’ storage or processing capacity. One can also overload the network to affect the system’s availability. Alternatively, the person will steal sensitive data and inject viruses into the system. It might be challenging to detect an internal threat, but watching out for suspicious behaviors among your staff can help.
11. Al-powered attacks
Artificial intelligence uses algorithmic processes to train computers to perform tasks on their own. That is achieved by making them repeat tasks, to learn about looming obstacles. Al can be used to hack into systems and cause significant damage. For instance, they can take control of drones and result in injuries, emotional harm, or even deaths. They also automate DoS attacks, password cracking, stealing money, and identity theft. Notably, large Al-powered attacks have managed to cut power supplies to entire regions, shut down hospital services, and affected national security.
Examples of cyberattacks of the 21st century
1. Adobe cyber attack
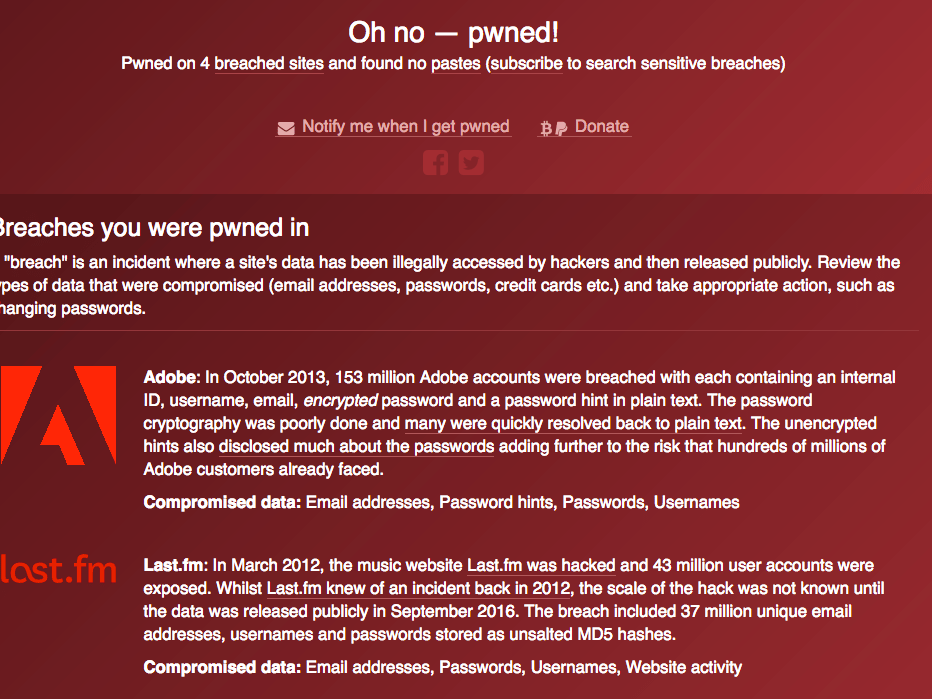
Have I Been Pwned? This site will tell you if your accounts have been compromised.
In October 2013, a cyberattack compromised the personal information of more than 38 million Adobe users. That included passwords, IDs, customers’ names, and credit and debit card information. Adobe Company was accused of biased business practices and violating the Customer Records Act. Consequently, the company had to pay $1 million in legal fees.
2. RSA security attack

In March 2011, hackers performed a successful phishing attack on RSA employees. They impersonated specific individuals and managed to gain access to the company’s network. The cybercriminals stole approximately 40 million employee records in the attack.
3. Cyberattack on Sony PlayStation network
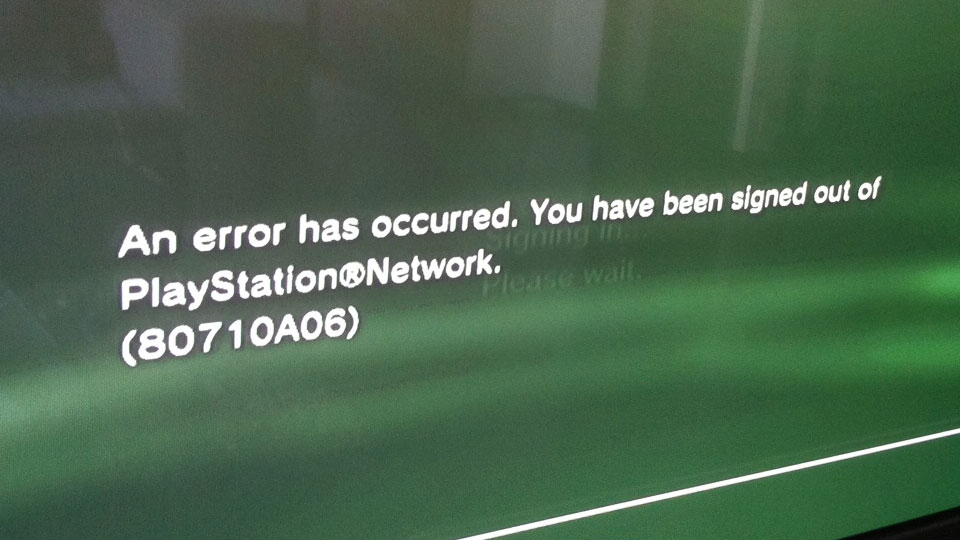
On April 20, 2011, Sony incurred losses of approximately $171 million. Initially, a lawsuit over the breach required the company to pay $15 million in reimbursement. The cybercriminals managed to hack 77 million Network accounts. Notably, the credit card numbers of 12 million accounts were not encrypted. Therefore, the hackers stole information about the users’ home addresses, purchase history, passwords, credit card numbers, emails, full names, and PSN/Qriocity logins.
4. US Office of Personnel Management (OPM) data breach
© ClearanceJobs
In 2012, a Chinese hacker gained access to the OPM system through a third-party contractor. However, the stakeholders discovered the issue in March 2014. In May of the same year, the system was hacked again. Similarly, the intrusion was detected about a year later. Notably, the cybercriminals stole sensitive information of more than 22 million past and current federal workers. The data included fingerprint information and security clearance data.
5. JP Morgan Chase data breach

In 2014, hackers gained unauthorized access to the bank servers of JP Morgan. They stole contact information of 7 million small businesses, 76 million households, and over 83 million accounts. That included their email addresses, phone numbers, addresses, and names. Luckily, JP Morgan did not incur any financial losses.
Notably, the attack happened when the hackers stole the login credentials of one of the employees. After that, they accessed one server that contained essential records. That is because the security team had not upgraded the network server with a two-factor password scheme. Fortunately, the security team stopped the hackers before they compromised the most sensitive customer information.
6. Uber cybersecurity breach

In late 2016, Uber discovered a data breach. However, the company only publicized it a year later. The hackers stole the driving license numbers of 600,000 Uber drivers. Additionally, the attack compromised email addresses, phone numbers, and names of 57 million users.
Uber offered the hackers $100,000 in exchange for the promise that they will destroy the data. However, they did not verify that the cybercriminals actually did it.
At the time of the breach announcement, Uber was in negotiations with Softbank over the sale of its stakes. The value of the deal went down to $48 billion from the previous $68 billion. Notably, the breach not only bore financial consequences for the company, but it also ruined Uber’s reputation.
7. Target Stores data breach

Photo of the statement from Target Chairman in the news.
Towards the end of December 2013, cybercriminals exploited the vulnerability of Target Stores’ private network. That happened through a third party vendor for the HVAC system to POS payment card readers. Notably, the hackers managed to steal the contact information and debit/credit card details of up to 110 million people. This cyberattack was a big blow to the company because it did cost them around $162 million. Following the breach, the CIO and CEO of the company resigned.
8. Equifax cyberattack

In 2017, a cyberattack on Equifax’s systems compromised the data of 143 million of its customers. Cybercriminals took advantage of an application vulnerability in the company’s site to launch the attack. The hackers accessed information like drivers’ license numbers, addresses, Social Security Numbers, and birth dates of Equifax customers. They also stole credit card information of about 209,000 customers. Equifax believes that the attack started in May, but the firm discovered it in July.
9. E-bay cyberattack

A message on the eBay Inc homepage yesterday urged customers to change their passwords in the wake of one of the biggest cyber attacks in history.
In May 2014, a hacker used the corporate employee’s accounts to gain access to the user’s database. For 229 days, the cybercriminals had complete access to E-bay’s network. They accessed encrypted passwords, addresses, dates of birth, and names of about 145 million users. Fortunately, customers’ financial data was not compromised because it was in a separate database. However, the company suffered significant losses and received criticism for the breach.
10. Cyberattack on Yahoo

In 2013-2014, a cyberattack compromised the security of 3 billion Yahoo user accounts. At stake was information like security questions and answers, passwords, email addresses, dates of birth, and names of the users. This attack had severe consequences for Yahoo because its value dropped from $100 billion to $4.48 billion. Following the breach, Yahoo decided to sell its core internet business to Verizon. And after the sale, its name changed to Altaba, Inc.
If companies like eBay, Yahoo, and Equifax can fall victim to a cyberattack, then anyone can. From the above examples, we have seen the value of established businesses dropping significantly after a breach. A successful attack can cost you a lot of money and impact your reputation negatively. Notably, it takes years to build a brand name globally, but a single event can bring it all down like a house of cards. However, you will be safer if you remain informed about the various types of cybercrimes. Don’t forget to adhere to all the safety measures on cybersecurity religiously.

