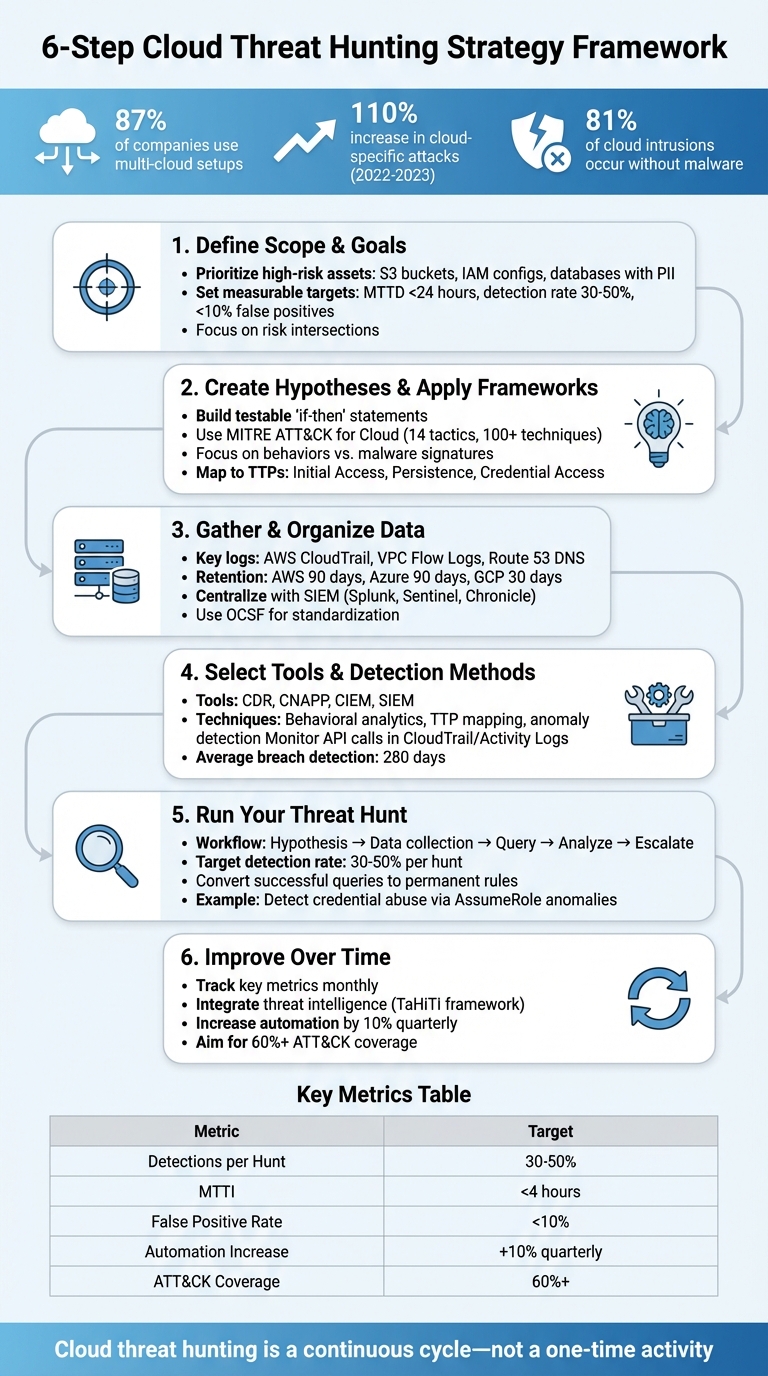
Cloud threat hunting is about actively searching for hidden threats in your cloud environment instead of waiting for alerts. With 87% of companies now using multi-cloud setups and cloud-specific attacks increasing by 110% from 2022 to 2023, this approach is critical. Attackers often exploit identity credentials and misconfigurations, bypassing traditional tools. A structured threat-hunting process can help detect these threats early.
Key Steps to Build Your Strategy:
- Define Scope: Focus on high-risk assets like S3 buckets, IAM configurations, and sensitive databases.
- Create Hypotheses: Use attacker behaviors (TTPs) and frameworks like MITRE ATT&CK for Cloud to guide your hunts.
- Organize Data: Centralize logs from AWS, Azure, and Google Cloud to ensure visibility.
- Select Tools: Use SIEMs, CNAPPs, and other tools to analyze telemetry and detect anomalies.
- Run Hunts: Test hypotheses, identify patterns, and escalate confirmed threats.
- Refine Process: Track metrics like detection rates and reduce false positives to improve over time.
Cloud threat hunting isn’t just about reacting to alerts – it’s a continuous process of monitoring, investigating, and improving defenses to stay ahead of attackers.
6-Step Cloud Threat Hunting Strategy Framework
Introduction to Cloud Threat Hunting | Types & Methodologies | Threat Hunting Loop
Step 1: Define Your Scope and Goals
To get started on the right foot, it’s crucial to define your scope. This step ensures your threat hunting efforts remain focused and proactive rather than devolving into unorganized alert-chasing. In cloud environments, this clarity is even more important due to the transient nature of resources like containers and serverless functions, which may only exist for minutes, leaving limited telemetry behind. A well-defined scope allows you to zero in on your most critical assets.
Prioritize Your Most Important Assets
Start by identifying the assets that are most vital to your organization – those whose compromise would cause the greatest damage. Focus on high-value areas such as cloud storage (think S3 buckets holding sensitive data), identity and access management (IAM) configurations, and databases containing personally identifiable information (PII). As CrowdStrike aptly puts it:
"Threat hunting efforts should be driven by risk, focusing first on the areas that would have the greatest impact on the organization if they were attacked."
Instead of chasing down every misconfiguration, prioritize what Wiz refers to as "risk intersections." These are scenarios where multiple vulnerabilities combine to create a significant attack path. For instance, an internet-facing S3 bucket containing PII, accessible via an application with administrative IAM permissions, presents a much higher risk than isolated issues. Using graph-based prioritization can help you map these multi-step relationships, such as identifying all internet-exposed resources that could access critical databases through overprivileged identities.
Set Goals Based on Business Risk
Once you’ve pinpointed your key assets, turn those priorities into actionable, risk-based objectives. Establish normal baselines for user access, API calls, and resource provisioning so you can quickly detect unusual activity. Align your detection rules with the MITRE ATT&CK for Cloud framework to identify any gaps in coverage. For example, you might find that while your "Initial Access" controls are strong, your "Persistence" defenses need improvement.
Set measurable targets to track your progress and maturity in threat hunting. Aim for metrics like a mean time to detect (MTTD) of under 24 hours for critical threats, a detection success rate of 0.3–0.5 per hunt, and coverage of at least 60% of relevant cloud techniques. Keep your false positive rate below 10%, as higher rates suggest your hypotheses need refinement. These benchmarks not only help you measure your progress but also guide the development of detection frameworks and playbooks for future hunts.
Step 2: Create Hypotheses and Apply Frameworks
Once you’ve identified your priority assets, the next step is to develop testable attack hypotheses. This ensures your threat-hunting efforts are focused and strategic. As Google Threat Intelligence puts it:
"The central concept of this approach is moving from simple Indicators of Compromise (IoCs) – which are static and quickly change – to Adversary Behaviors defined by Tactics, Techniques, and Procedures (TTPs)."
These hypotheses form the foundation for a more targeted and data-driven approach to identifying threats.
Building Hypotheses from Threat Indicators
You can craft hypotheses by analyzing three key sources: intelligence on attacker TTPs, tactical insights into known attack indicators, and anomalies flagged by analytics. The goal is to create specific, testable "if-then" statements. For instance: "If an attacker has stolen credentials, then we should observe sts:AssumeRole calls originating from unusual ASNs or countries outside our baseline."
Shift your focus to behaviors specific to cloud environments rather than traditional malware signatures. With 81% of hands-on-keyboard cloud intrusions now occurring without malware, it’s critical to monitor for patterns like identity sprawl, API-driven attacks targeting management interfaces, or fleeting anomalies in containers and serverless functions. Additionally, findings from Cloud Security Posture Management (CSPM) tools can highlight "toxic combinations", such as internet-exposed resources paired with administrative permissions.
Leveraging MITRE ATT&CK for Cloud
The MITRE ATT&CK for Cloud framework offers a structured way to approach threat hunting, organizing threats into 14 tactics and over 100 cloud-specific techniques. Use this framework to map your hypotheses to relevant techniques. For example, if you suspect credential abuse, focus on T1078.004 (Valid Accounts) and examine logs for unusual sts:AssumeRole activity.
This framework also helps identify detection gaps. For instance, you might have solid coverage for Initial Access techniques but limited visibility into Persistence tactics like T1098.001 (Account Manipulation), where attackers could exploit overly permissive policies to maintain access. By identifying such gaps, you can allocate hunting resources more effectively, prioritizing areas with the highest risk and least coverage.
Step 3: Gather and Organize Your Data
Once you’ve outlined your hypotheses, it’s time to gather the right data to bring your strategy to life. Collecting and correlating essential logs across cloud platforms is crucial. This step ties directly back to your hypothesis development, laying the groundwork for meaningful analysis.
Which Cloud Logs to Track
Start by focusing on three key log sources: AWS CloudTrail (API activity), VPC Flow Logs (network traffic), and Route 53 Resolver query logs (DNS activity). These logs provide the baseline visibility needed for most investigations.
- Management plane logs capture infrastructure changes (like creating an EC2 instance).
- Data plane logs monitor actions within services (like reading an S3 file).
"CloudTrail logs act like activity trails, capturing activity across your AWS environment. They’re essential for both understanding what happened during an incident and building detections to catch threats early." – Tamara Chacon, Member of Splunk’s SURGe team
Keep in mind that log retention policies vary by cloud provider. For example:
- AWS CloudTrail management events retain data for 90 days unless specific trails are configured.
- Azure Activity Logs are deleted after 90 days.
- Google Cloud retains non-admin logs for just 30 days.
For identity-related telemetry, which is critical for spotting credential abuse, monitor:
- Microsoft Entra ID Sign-in/Audit logs
- AWS IAM credential reports
- Google Cloud Identity logs.
If you’re working with containers or serverless functions, selectively enable data events for high-value assets. This approach helps manage costs while still capturing critical details like process executions and file integrity changes.
Centralize Data for Better Analysis
Once you’ve identified the logs you need, centralizing them is the next step. Aggregating logs from all cloud providers into a single platform eliminates blind spots and simplifies analysis. Using a SIEM like Splunk, Microsoft Sentinel, or Chronicle can help streamline this process. Tools like the Open Cybersecurity Schema Framework (OCSF) can standardize data from AWS, Azure, and GCP, ensuring consistency in fields like timestamps and user identities for better cross-platform correlation.
To automate log collection, leverage Infrastructure as Code tools like AWS CloudFormation to enable and gather logs across accounts. Depending on your needs:
- Use pull methods (e.g., S3 + SQS) to handle large volumes of data.
- Opt for push methods (e.g., Kinesis Firehose) for real-time detection.
Store "hot" data in your SIEM for short-term analysis (30–90 days) and archive "cold" data in services like Amazon S3 or Azure Archive Storage for long-term review. Regularly validate your ingestion pipelines to ensure they’re functioning correctly and capturing the necessary fields – like sourceIPAddress or userIdentity – to support your hypotheses.
sbb-itb-760dc80
Step 4: Select Tools and Detection Methods
Now that your data is centralized and properly organized, it’s time to focus on choosing the tools and methods to identify potential threats. This step builds on your data strategy, and selecting the right tools can make all the difference in detecting threats efficiently. With the growing complexity of cloud environments, today’s cloud security tools offer layered defenses that align with the challenges you face.
Cloud Threat Hunting Tools Overview
Using your centralized log data effectively requires the right tools. Your choice should depend on the types of threats you’re aiming to detect and the specific cloud platforms you’re protecting. Here’s a breakdown of key tools:
- Cloud Detection & Response (CDR) platforms: These tools analyze telemetry from networks, endpoints, and applications to identify threats in real time.
- Cloud-Native Application Protection Platforms (CNAPP): These platforms combine workload protection with security posture management, helping you identify both configuration risks and runtime threats.
- Cloud Infrastructure Entitlement Management (CIEM): Ideal for identity-focused hunting, these tools tackle risks related to excessive permissions and unauthorized access.
- SIEM: Still a cornerstone for centralized log analysis, SIEM tools provide the historical data needed for forensic investigations.
Cloud intrusions have surged by 75% between 2022 and 2023, with attacks by "cloud-conscious" threat actors – those exploiting cloud-specific features – rising by 110% in the same period. With 87% of organizations now operating in multi-cloud environments, achieving unified visibility is no longer optional.
When evaluating tools, prioritize those that scale with your telemetry, offer real-time monitoring, and leverage behavioral analytics for areas like IAM, storage, and serverless functions. Integration is equally important – your tools must work seamlessly with your existing SIEM, threat intelligence feeds, and incident response workflows. Modern solutions are increasingly adopting agentless scanning and eBPF sensors to monitor containers, tracking both process executions and network connections.
Detection Techniques That Work
Once you’ve selected your tools, the next step is implementing detection techniques that maximize their capabilities. Successful threat hunters rely on strategies like behavioral analytics, TTP mapping, and anomaly detection:
- Behavioral analytics: This technique identifies what "normal" behavior looks like for users, service accounts, and cloud entities, flagging deviations that might slip past traditional signature-based defenses.
- TTP mapping: Aligning detections with the MITRE ATT&CK framework for Cloud helps you cover the full attack lifecycle.
- Anomaly detection: Machine learning-powered anomaly detection can uncover outliers that manual analysis might miss.
"Threat hunting involves hypothesizing about attackers’ behavior and verifying the hypotheses in your environment… Using IoCs to search for an attacker’s persistence is not." – Jamie Butler, Tech Lead, Elastic Security
A key focus should be cloud control plane monitoring – examining API calls in logs like AWS CloudTrail or Azure Activity Logs. Cross-domain correlation is also crucial. For example, in May 2024, the threat group SCATTERED SPIDER (responsible for 29% of cloud-based intrusions tracked by CrowdStrike in 2023) breached a cloud-hosted VM. They started by phishing credentials to access the cloud control plane, then used a VM management agent to execute commands. CrowdStrike detected them by correlating control plane telemetry with VM-level detections.
Some practical detection tactics include monitoring for ConsoleLogin events where mfaAuthenticated is false, especially for privileged accounts. Similarly, look for errorCode=AccessDenied patterns, which can indicate compromised accounts testing their access limits. Machine learning can also help establish a baseline for API call frequencies, flagging unusual spikes that might signal automated discovery or data exfiltration attempts. With breaches taking an average of 280 days to identify and contain, automation and AI-driven analytics can significantly reduce this timeframe. By automating routine tasks like log aggregation and data normalization, your team can focus on more complex and high-stakes investigations.
Step 5: Run Your Threat Hunt
With your tools and detection methods ready, it’s time to execute your threat hunt. Following a structured workflow – from hypothesis to response – can significantly reduce the time it takes to detect breaches. This is especially important since over 20% of reported breaches are still identified by third parties rather than the victim organization’s own teams.
The Threat Hunting Workflow
A successful threat hunt relies on a repeatable process. Start by crafting a clear and specific hypothesis to guide your investigation. This hypothesis should be based on threat intelligence, unusual behavior patterns, or gaps in your MITRE ATT&CK framework coverage.
Next, gather and normalize data from sources like AWS CloudTrail, Azure Activity Logs, and identity provider logs. Use targeted queries to identify anomalies and deviations from your baseline behaviors. Focus on anomalies that are both rare and recent to shorten the time attackers can operate undetected. Eliminate unnecessary "noise" by filtering out results with zero or N/A values to focus on meaningful changes.
When you find suspicious activity, analyze it using User and Entity Behavior Analytics (UEBA) to determine if the behavior is benign or malicious. Use "bookmarks" to save specific results, queries, and timeframes for evidence collection. If a threat is confirmed, escalate the issue to your incident response team. Attach the relevant evidence, then take containment actions like isolating compromised resources, revoking overprivileged IAM roles, or rotating access keys.
Turn successful hunt queries into permanent detection rules. Add indicators of compromise – such as malicious IPs or file hashes – to your threat intelligence feeds. Ideally, aim for a detection success rate of 30–50% per hunt, converting effective queries into long-term detection mechanisms.
Example Playbook: Detecting Credential Abuse
To illustrate, let’s apply this approach to a common threat: credential abuse. This is one of the most frequent cloud threats, as attackers often exploit compromised IAM credentials to move laterally within the cloud control plane instead of deploying traditional malware.
Begin with a hypothesis. Map it to MITRE ATT&CK technique T1550.001 (Use Alternate Authentication Material: Application Access Token). Your primary data source will be AWS CloudTrail, specifically monitoring sts:AssumeRole management events.
Run a query to identify AssumeRole calls originating from new Autonomous System Numbers (ASNs) or countries not in your baseline. If you detect unusual activity, use UEBA to analyze whether the entity has accessed these resources before. Review the User-Agent string and check the IAM policies tied to the role to understand the attacker’s level of access.
For containment, add the malicious IP to your threat intelligence platform and create an automated detection rule to flag similar anomalies in the future. Look for "toxic combinations" where the compromised identity had access to sensitive data, such as S3 buckets with personally identifiable information. Conduct a root cause analysis to pinpoint the weakness that enabled the breach – like overly permissive IAM roles or missing multi-factor authentication requirements.
| Detection and Response Phases | Key Actions | Cloud-Specific Considerations |
|---|---|---|
| Containment | Isolate hosts, revoke tokens, disable APIs | Account for the behavior of ephemeral resources |
| Eradication | Remove malicious functions, patch images, rotate keys | Update Infrastructure as Code (IaC) templates |
| Recovery | Restore from verified clean snapshots, check IAM configurations | Ensure no persistence in cloud management consoles |
| Improvement | Develop new detection rules, enhance threat intelligence feeds | Align findings with MITRE ATT&CK for Cloud |
Step 6: Improve Your Process Over Time
With a structured threat-hunting workflow in place, it’s crucial to keep refining your approach. Threat hunting isn’t a one-and-done activity – it’s an ongoing cycle of learning and adapting to stay ahead of attackers.
The threat landscape is constantly shifting. For instance, cloud intrusions increased by 26% in 2024, and incidents involving "cloud-conscious" threat actors skyrocketed by 110% between 2022 and 2023. Attackers are increasingly exploiting cloud-specific features like auto-scaling and identity-based access, which means your strategies need to evolve just as quickly.
Integrate Threat Intelligence
External threat intelligence feeds can provide valuable direction and context for your hunts. Instead of running generic searches, frameworks like TaHiTI (Targeted Hunting integrated with Threat Intelligence) help zero in on behaviors specific to threat actors in your industry. To identify gaps in your defenses, review your MITRE ATT&CK coverage. For example, if you have strong detection for "Initial Access" but weaker coverage for "Persistence", prioritize hunts targeting those blind spots.
Blend external intelligence with internal insights, such as data from past incidents, cloud configuration risks, and third-party dependencies. Open source intelligence (OSINT) can also be a rich source of indicators like malicious IPs or domain hashes – integrate these into your workflow. Even if a hunt doesn’t uncover an immediate threat, it should still contribute to better detection rules and stronger preventive measures.
Track Metrics and Adjust Your Approach
Measuring the effectiveness of your threat-hunting program is essential for understanding what works and what needs improvement. Here are some key metrics to monitor:
- Detections per Hunt: Aim for a target rate of 0.3–0.5 (30–50%). A low rate could mean your hypotheses need refining, while a very high rate might indicate you’re chasing known alerts rather than proactively uncovering new threats.
- Mean Time to Investigate (MTTI): Keep this under 4 hours per hunt. If this number starts climbing, it might signal the need for better training, improved tools, or more organized data.
- False Positive Rate: Aim for less than 10%. High rates suggest your hypotheses are too broad or your data lacks sufficient context.
- Automation Percentage: Strive to increase this by 10% each quarter, transitioning from manual hunts to automated processes.
- ATT&CK Technique Coverage: Set a maturity goal of 60% or higher to ensure you’re addressing a wide range of cloud-specific tactics.
| Metric | Target Goal | What It Tells You |
|---|---|---|
| Detections per Hunt | 0.3–0.5 (30–50%) | Low rates suggest poor hypotheses; very high rates may indicate reactive hunting |
| Mean Time to Investigate (MTTI) | < 4 hours | Increasing time signals a need for better training, tool integration, or organized data logs |
| False Positive Rate | < 10% | High rates indicate hypotheses are too broad or data lacks sufficient context |
| Automation Percentage | +10% quarterly | Tracks maturity progression toward automated, repeatable hunting |
| ATT&CK Coverage | 60%+ | Identifies blind spots where new hunts should be prioritized |
Review these metrics monthly to identify bottlenecks and areas for improvement. When a hunt successfully identifies a threat, turn that logic into a permanent analytic rule in your SIEM or Cloud Detection and Response (CDR) platform. This not only strengthens your defenses but also helps you gradually shift from manual processes to automated, repeatable ones. Use these insights to fine-tune your detection rules and build on the automation you’ve already introduced.
Conclusion: Maintain Strong Cloud Security
Staying ahead of attackers in the cloud requires an ongoing commitment to proactive threat hunting. This guide has walked you through defining the scope, forming hypotheses, gathering data, choosing the right tools, executing hunts, and refining your approach. The goal? Turning these steps into a continuous and actionable defense strategy.
Cloud threats are evolving at an incredible pace. Attackers are becoming more resourceful, exploiting cloud-specific features like auto-scaling and IAM credentials. Every hunt you conduct provides new insights that help fine-tune your security measures.
With these insights, treat threat hunting as a continuous cycle. Regularly review your metrics – monthly assessments can help pinpoint bottlenecks. Update your hypotheses to reflect changes in your environment, and map your coverage against the MITRE ATT&CK for Cloud framework to uncover any gaps. As Benjamin McInnis, Technical Marketing Manager at CrowdStrike, explains:
Cloud threat hunting is the proactive process of identifying potential cyber threats within cloud environments before they evolve into full-blown security breaches.
This proactive approach is what sets apart organizations that merely react from those that actively prevent incidents.
To keep your strategy effective and adaptable, automate routine tasks so your team can focus on deeper, more complex analyses. Collaborate across departments – sharing findings with Incident Response, DevOps, and IT operations ensures your discoveries lead to meaningful improvements. Make room for proactive threat hunting, not just responding to alerts. The effort you invest today reduces risk and speeds up threat detection in the future. By committing to a cycle of constant review and adaptation, your organization can stay ahead of the ever-changing landscape of cloud threats.
FAQs
How does cloud threat hunting enhance security?
Cloud threat hunting shifts your security strategy from simply reacting to incidents to actively seeking out hidden dangers in your cloud environment. This proactive approach helps you spot potential threats early, enhances your detection abilities, reduces risks, and bolsters your overall security defenses.
To begin, start by crafting hypotheses specific to your cloud setup. Use data sources like API logs and container runtime events to gather insights, and actively search for unusual activity or patterns. The insights gained from these hunts can then be used to fine-tune detection rules, adjust policies, and set up automated responses, ensuring your defenses evolve continuously.
By taking this structured and forward-thinking approach, you can uncover threats that traditional tools might overlook, safeguarding your cloud workloads and reinforcing your security framework.
What are the best practices for managing and centralizing cloud logs effectively?
To manage and centralize cloud logs effectively, start by establishing a clear log collection policy. This policy should outline all necessary sources, such as access logs, API activity, and network traffic, while ensuring alignment with compliance standards and data classification requirements.
Next, centralize your logs in a secure, tamper-proof repository. Use write-once/read-many (WORM) controls to safeguard logs from unauthorized changes. Standardizing log formats and naming conventions will make analysis more straightforward, while implementing role-based access controls (RBAC) will ensure only authorized users can access sensitive data.
Leverage cloud-native tools to automate both log collection and enrichment processes. Integrate your logs with a Security Information and Event Management (SIEM) system for real-time monitoring and analysis, helping to quickly identify potential threats. Finally, make it a habit to regularly review and refine your logging practices to keep up with evolving threats and changing business needs.
These steps help ensure your cloud logs are not only secure and well-organized but also ready to support proactive threat detection and response.
How can I prioritize assets for effective threat hunting in a multi-cloud environment?
To effectively prioritize assets for threat hunting in a multi-cloud setup, start by building a comprehensive inventory of your cloud resources across platforms like AWS, Azure, and GCP. Make sure to include everything – compute resources, storage, databases, and networking components. Assign tags to each asset that capture essential details such as the business owner, the environment (e.g., production or development), and the data classification.
Once you have your inventory, evaluate each asset based on its importance to business operations and the sensitivity of the data it handles. High-priority assets often include those tied to customer-facing applications, payment systems, or those storing regulated data like PHI. Pay close attention to assets with higher exposure levels, such as those with public endpoints, open APIs, or overly permissive access settings, as they are more likely to be targeted.
Lastly, verify that all assets are equipped with sufficient logging and telemetry to support effective threat detection. Use a combination of factors – business criticality, exposure, and telemetry coverage – to assign a priority score to each asset. Focus your threat-hunting efforts on the assets with the highest scores. Keep in mind that your cloud environment and the threat landscape are constantly evolving, so make sure to regularly revisit and update your prioritization strategy.

