Why Cyber? Check Out Our Articles!
Worried about online threats? Use our free Cybersecurity Risk Calculator
Proactive cloud threat hunting finds identity misuse and misconfiguration risks
Checklist for preparing, activating, and managing secure incident response communications
Create a tailored cybersecurity policy for your business in minutes!
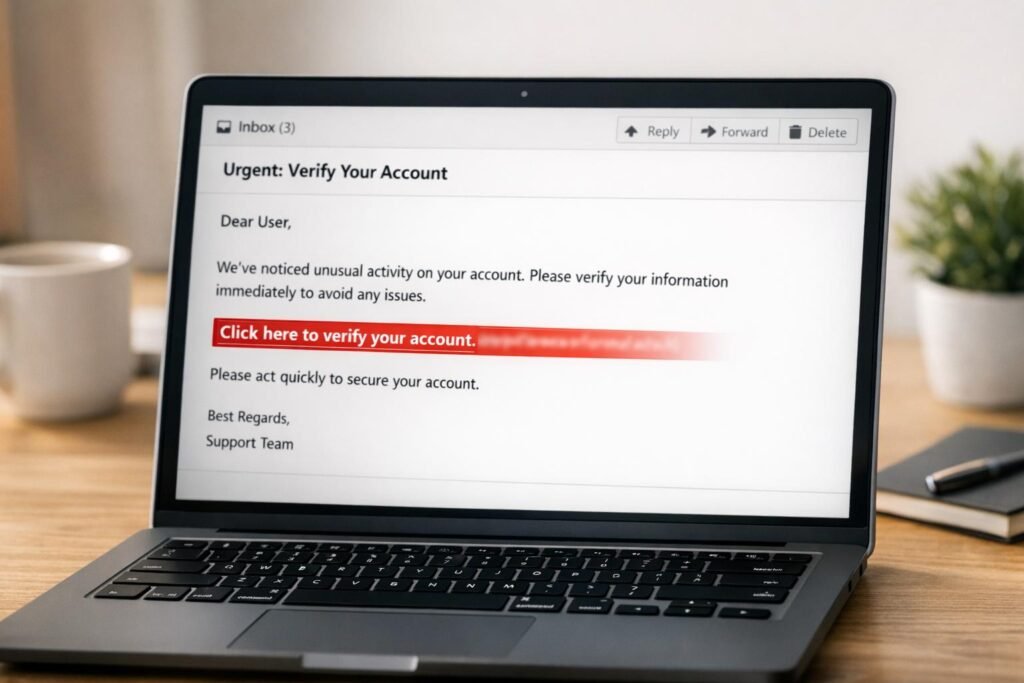
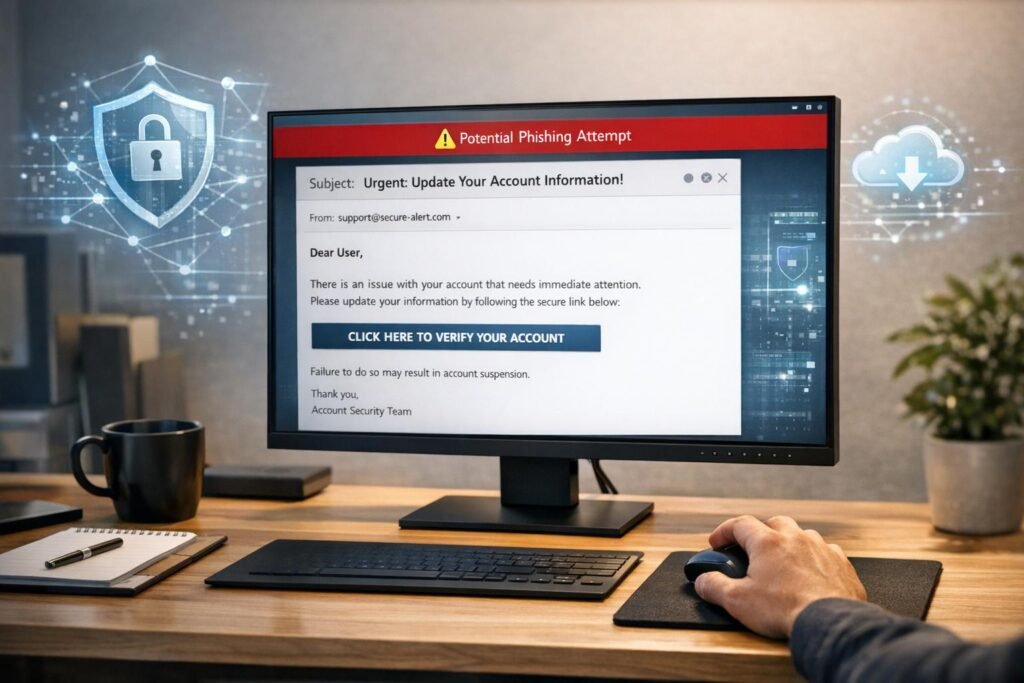
Make phishing reporting easy: add one-click channels, run short simulations,
Realistic phishing simulations and AI-driven training can cut employee susceptibility
Understand the six-phase threat intelligence lifecycle — planning, collection, processing,