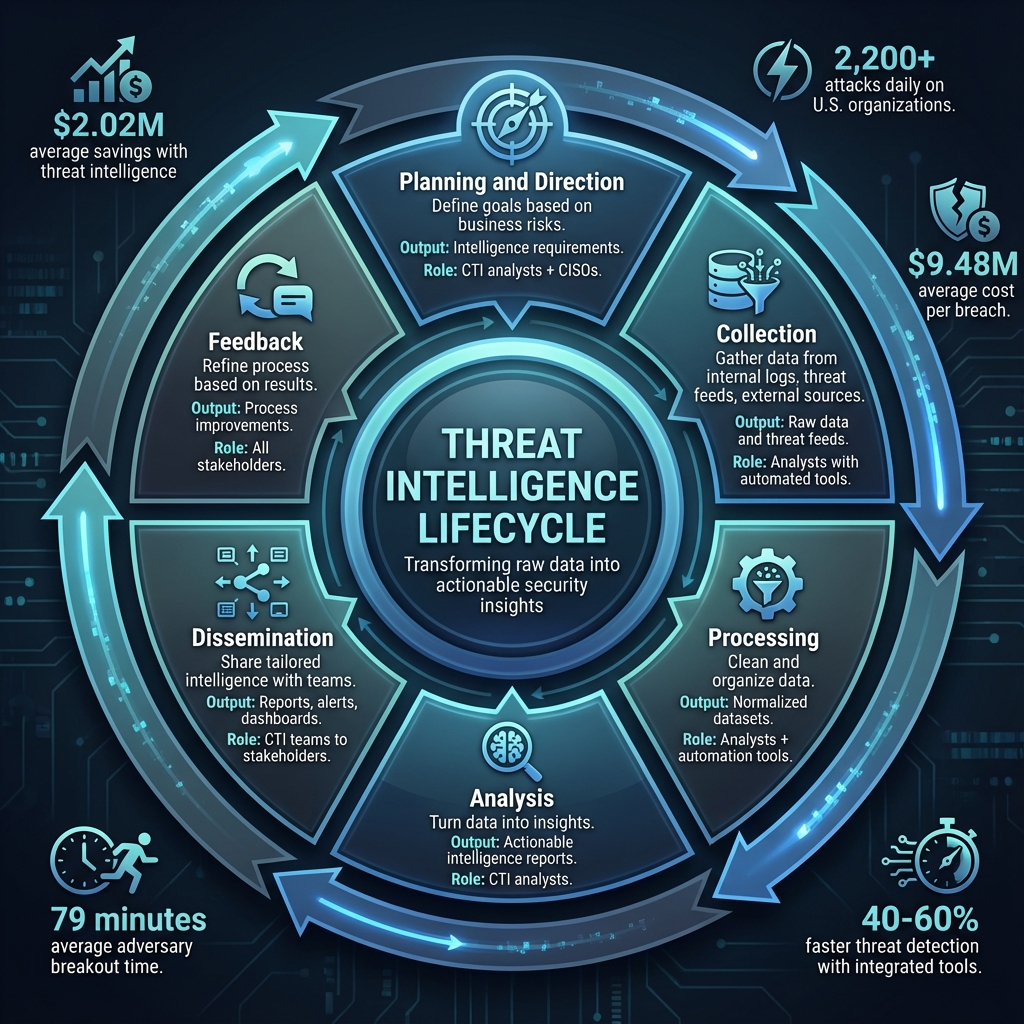
Cyber threats are relentless, with U.S. organizations facing over 2,200 attacks daily, costing an average of $9.48 million per breach. Managing this risk requires more than just raw data – it demands a structured process to transform information into actionable insights. This is where the Threat Intelligence Lifecycle comes in.
The lifecycle breaks down into six phases that help organizations identify threats, analyze risks, and respond effectively:
- Planning and Direction: Define goals based on business risks and priorities.
- Collection: Gather data from internal logs, threat feeds, and external sources.
- Processing: Clean and organize data for meaningful analysis.
- Analysis: Turn data into insights, such as identifying attacker methods.
- Dissemination: Share tailored intelligence with teams for action.
- Feedback: Refine the process based on results and stakeholder input.
This approach helps detect threats earlier, reduce response times, and align security efforts with business needs. With tools like TIPs, SOAR platforms, and frameworks like MITRE ATT&CK, teams can streamline each phase and focus on high-priority risks. Whether you’re tracking ransomware groups or identifying vulnerabilities, the Threat Intelligence Lifecycle ensures your efforts are efficient and effective.
The 6 Phases of the Threat Intelligence Lifecycle
Cyber Threat Intelligence – CTI Lifecycle, CTI Types, Attack Lifecycle, Models and Reports
The 6 Phases of the Threat Intelligence Lifecycle
The threat intelligence lifecycle is a structured process that transforms raw data into actionable decisions, reducing risk and adapting to evolving threats. Each phase plays a specific role, with defined inputs, outputs, and responsibilities. This cycle is iterative – feedback from one round informs and improves the next. Here’s a breakdown of these six phases and how they work together.
Phase 1: Planning and Direction
This is where it all begins. Planning sets the stage by aligning intelligence efforts with business priorities and risks. Your team identifies what’s most critical to your organization and defines intelligence goals.
- Purpose: Align intelligence efforts with business objectives, prioritizing based on risk and compliance needs.
- Key Inputs: Business goals, risk tolerance, compliance requirements, and an understanding of the threat landscape.
- Key Outputs: Defined intelligence requirements, prioritized threat lists, and a clear collection plan.
- Primary Roles: CTI analysts work closely with CISOs, risk teams, and business leaders to identify critical assets and threats.
For example, a hospital network might focus on ransomware groups targeting healthcare, creating an intelligence requirement like: “Identify ransomware affiliates selling access to U.S. healthcare networks and document their methods.” A financial institution, on the other hand, may prioritize credential theft schemes affecting online banking.
Best practices include documenting key threat actors, narrowing the focus to the top three to five risks, and regularly reviewing priorities – either quarterly or after major incidents – to ensure alignment with evolving threats.
Phase 2: Collection
With a clear plan in place, the next step is gathering the data needed to meet your intelligence requirements. This phase pulls information from internal and external sources to create a foundation for analysis.
- Purpose: Gather data that supports the defined intelligence goals.
- Key Inputs: Intelligence requirements and the collection plan from Phase 1.
- Key Outputs: Raw data, logs, threat feeds, and advisory reports.
- Primary Roles: Analysts use both automated tools and manual methods to collect data from diverse sources.
Internal sources might include firewall logs, EDR telemetry, SIEM alerts, vulnerability scans, and email gateway logs. External data could come from OSINT (e.g., social media or public databases), commercial threat feeds, government advisories (like CISA or FBI), ISACs, and dark web monitoring.
For instance, if the goal is tracking initial access brokers targeting healthcare, you might collect data from TOR forums, CISA healthcare vulnerability alerts, and commercial feeds identifying ransomware infrastructure.
To ensure success, diversify your sources, automate collection when possible, and evaluate each source for timeliness, reliability, and cost.
Phase 3: Processing and Analysis
Raw data is often messy. This phase focuses on cleaning, organizing, and enriching that data to uncover meaningful insights.
- Purpose: Transform raw data into structured, actionable intelligence.
- Key Inputs: Data gathered during the collection phase.
- Key Outputs: Normalized datasets, enriched threat profiles, mapped adversary tactics, and actionable intelligence reports.
- Primary Roles: Analysts utilize tools and frameworks to clean, enrich, and analyze data, turning it into clear insights.
During processing, data is cleaned, deduplicated, and standardized into formats like STIX or JSON. Enrichment might involve WHOIS lookups, passive DNS queries, or reputation checks. Analysis then connects the dots, identifying patterns or linking indicators to specific campaigns using established frameworks.
To maximize effectiveness, use confidence scoring to assess reliability, automate repetitive tasks, and validate findings through multiple sources. Tailor the results for different audiences: SOC analysts may need tactical feeds, while executives benefit from strategic overviews.
Phase 4: Dissemination and Feedback
Intelligence only matters if it reaches the right people in a format they can use. This phase ensures the intelligence is shared effectively and incorporates feedback to refine future efforts.
- Purpose: Deliver actionable intelligence to stakeholders and collect feedback to improve the process.
- Key Inputs: Finished intelligence products from the analysis phase.
- Key Outputs: Reports, alerts, dashboards, tickets, and playbooks tailored to specific teams.
- Primary Roles: CTI teams distribute intelligence securely to relevant stakeholders, who then provide feedback.
For example, SOC teams might receive machine-readable feeds integrated into SIEM or EDR systems, while executives might prefer concise visual reports highlighting business risks. IT teams benefit from step-by-step remediation guides with clear deadlines.
Feedback is critical. Use stakeholder surveys, post-incident reviews, and performance metrics (like detection update times) to evaluate the intelligence’s relevance and usability. This feedback loops back into planning and collection, ensuring the cycle continuously improves.
Tools and Resources for Each Phase
Matching Tools to Lifecycle Phases
The threat intelligence lifecycle becomes actionable when paired with the right tools. Each phase has unique requirements, and aligning tools to these needs determines how effectively your team can respond.
Threat Intelligence Platforms (TIPs) are central to multiple phases. Tools like MISP and Recorded Future help prioritize high-risk indicators by connecting intelligence objectives to business risks. During the collection phase, these platforms gather data from sources such as the open web, deep web forums, and dark web marketplaces, cutting down on manual effort. For processing, TIPs handle tasks like normalization, filtering, and enrichment automatically.
SOAR platforms – examples include Palo Alto Cortex XSOAR and Splunk Phantom – take automation further by managing processing and analysis. They run playbooks to score threats, align adversary tactics with MITRE ATT&CK frameworks, and build behavioral profiles. When TIPs and SOAR platforms are integrated, they can cut threat detection and response times by 40–60%, thanks to faster processing and more accurate dissemination. For dissemination, SOAR platforms automate tasks like sending tailored alerts to SOC teams, creating executive dashboards for leadership, and generating remediation tickets for IT teams, while also collecting feedback to refine future cycles.
SIEM systems like Splunk and ELK Stack shine during the analysis phase, especially in correlating internal logs with external threat feeds to identify patterns of malicious behavior. For smaller teams just starting out, open-source TIPs like MISP provide a cost-effective way to manage planning and collection. As operations expand, commercial SOAR solutions can scale to handle more complex analysis and dissemination needs.
Integration is critical. When tools operate in silos, up to 30% of intelligence can be wasted as data falls through the cracks between phases. To avoid this, prioritize platforms with strong API connectivity and built-in MITRE ATT&CK mapping. This ensures smooth data flow from collection to feedback, enabling more effective decision-making and stronger strategic insights, as highlighted by Cyber Detect Pro.
Using Cyber Detect Pro for Threat Intelligence

While tools handle the heavy lifting of data processing, Cyber Detect Pro bridges the gap between technical analysis and strategic planning. This resource enhances threat intelligence by providing expert insights and actionable context. For example, the blog covers emerging threats like ransomware campaigns and AI-driven attacks, helping teams focus on high-priority risks during the planning phase.
In the collection phase, articles such as "Best Practices for Using AI in OSINT" guide teams on leveraging artificial intelligence to improve open-source intelligence efforts. For non-technical stakeholders, content like "OSINT Training for Non-Tech Professionals" helps business leaders understand the intelligence requirements they’re approving, ensuring alignment across teams.
Cyber Detect Pro also supports the analysis phase with detailed, industry-specific threat breakdowns. Covering sectors like healthcare, banking, and retail, these insights go beyond raw indicators to explain adversary motivations and tactics. Founder Ken Adams, with over 20 years of cybersecurity experience, provides updates that help analysts quickly profile new threats, such as ransomware variants or credential theft schemes, and make informed decisions.
sbb-itb-760dc80
Common Challenges and How to Overcome Them
Challenges You’ll Face
Even with advanced tools, many U.S. organizations encounter obstacles that hinder the effectiveness of their threat intelligence programs. One of the biggest hurdles is data overload. Security teams often gather massive amounts of raw indicators, but without proper filtering, critical threats can get buried in the noise. This issue becomes even more complex when tools produce outputs that lack standardization, making it harder to accurately correlate and analyze data.
Another common problem is misaligned requirements during the planning phase. When CTI teams collect generic data instead of focusing on specific business risks – like protecting patient records in healthcare or preventing wire fraud in banking – their reports often go unused by executives or SOC teams. Without clarity on what matters most to the organization, intelligence efforts lose direction and fail to deliver actionable insights.
A significant gap also exists in the operationalization of intelligence. While teams may generate polished threat reports, these often fail to make their way into SIEM rules, firewall configurations, or incident response playbooks. As a result, the intelligence remains theoretical and doesn’t translate into practical security measures.
Lastly, a lack of stakeholder buy-in and poor feedback loops can further weaken the process. Intelligence outputs that aren’t tailored to their audience often go unread – executives need concise summaries that highlight financial implications, while SOC analysts require actionable details. Without proper alignment, feedback is stifled, and the program’s overall effectiveness suffers.
Addressing these challenges requires a structured, disciplined approach throughout each phase of the threat intelligence lifecycle.
Best Practices for Each Phase
To tackle these challenges, organizations need to focus on improving each stage of the lifecycle. During Planning and Direction, maintain a dynamic requirements document that aligns with critical assets and regulatory obligations. Collaborate with teams across security, risk, legal, and business functions to prioritize needs (e.g., high, medium, or low) and update them regularly – especially after major incidents or emerging threats like AI-driven attacks. Tools like Cyber Detect Pro can help track sector-specific trends, such as ransomware targeting particular industries, and adjust collection priorities accordingly.
In the Collection and Processing phase, clearly define the scope of data collection based on documented requirements. Focus on reliable sources like ISACs and commercial threat feeds, and automate processes to normalize, deduplicate, and enrich data with confidence scores. Using frameworks like MITRE ATT&CK can help quickly separate critical indicators from less relevant ones.
For the Analysis phase, add context to raw indicators by correlating data from multiple sources, mapping findings to TTPs (tactics, techniques, and procedures), and linking them to business processes. Provide prioritized recommendations with clear, actionable steps that stakeholders can implement effectively.
When it comes to Dissemination and Feedback, tailor your outputs to meet the needs of different audiences. SOC teams benefit from real-time alerts, executives need brief summaries focused on financial impact, and IT teams require detailed, actionable guidance. Create feedback loops through post-incident reviews, workshops, or quick surveys to gather input. Track metrics, such as CTI alerts that lead to successful threat detections, to demonstrate value and identify areas for improvement.
Conclusion
Key Takeaways
The threat intelligence lifecycle operates as a continuous, evolving process: planning, collection, processing, analysis, dissemination, and feedback. Each stage transforms raw data into meaningful insights, enabling quicker detection, shorter response times, and a stronger defense against cyberattacks. According to IBM‘s 2024 report, incorporating threat intelligence into your strategy can reduce breach costs by an average of $2.02 million.
To make the most of this lifecycle, disciplined execution and consistent feedback are key. Start by defining clear, documented requirements that align with your most critical assets and the unique risks of your industry. When collecting data, prioritize reliable and relevant sources to avoid overwhelming your systems with unmanageable volumes of information. During the analysis phase, focus on answering critical questions: What’s happening? Why does it matter? What steps should we take? Tailor your findings to your audience – technical teams need detailed, actionable insights, while executives require a focus on business impact.
Feedback plays a vital role in refining your approach. After incidents or routine evaluations, revisit your requirements, fine-tune your data sources, and adjust your detection rules based on lessons learned. Tools like Cyber Detect Pro can help your team stay ahead of emerging threats, from AI-driven attacks to ransomware targeting specific U.S. industries. These insights can then be translated into updated intelligence requirements, SIEM rules, and incident response plans.
The lifecycle is adaptable to organizations of all sizes. Smaller businesses can focus on a few key priorities and leverage managed services or curated threat intelligence sources, while larger enterprises may adopt more formalized, segmented programs across various departments. It’s essential to view threat intelligence as a strategic business function that safeguards revenue, reputation, and operations – not just a technical task. With CrowdStrike reporting that adversary breakout time now averages just 79 minutes, a structured, lifecycle-driven approach is critical to staying ahead of today’s rapidly evolving threats.
FAQs
How can organizations set priorities for intelligence goals during the Planning and Direction phase?
To effectively prioritize intelligence goals, organizations should align them with their most pressing objectives and security requirements. Begin by pinpointing key assets – like sensitive data or critical infrastructure – and evaluating the current threat environment to identify potential risks.
Concentrate on areas where the stakes are highest, and set specific, measurable goals to steer intelligence gathering and analysis. This approach ensures resources are allocated wisely and intelligence activities contribute directly to the organization’s broader security strategy.
What are the key tools for automating the Collection and Processing stages in threat intelligence?
To simplify the Collection and Processing stages in the threat intelligence lifecycle, tools like Security Information and Event Management (SIEM) systems, Threat Intelligence Platforms (TIPs), and Automated Threat Hunting tools are essential. These technologies handle real-time data collection, correlation, and analysis, making workflows faster and more efficient.
On top of that, Data Enrichment tools add vital context to raw data, making it more actionable for identifying and responding to threats. By using these tools, organizations can tackle emerging cyber threats with less reliance on manual processes.
How does feedback enhance the Threat Intelligence Lifecycle?
Feedback is a key component in reinforcing the Threat Intelligence Lifecycle, ensuring ongoing improvement at every stage. It enables organizations to pinpoint flaws in their detection and response systems, adjust to new and evolving threats, and refine their strategies to better manage potential risks.
When teams analyze feedback, they can identify shortcomings in their threat intelligence efforts, optimize tools and techniques, and adopt a more proactive stance toward cybersecurity. This continuous cycle of learning and adjustment helps maintain a stronger defense against emerging challenges.

