Managing vulnerabilities means identifying and fixing security flaws to reduce the risk of cyberattacks. There are two main strategies: Risk-Based Vulnerability Management (RBVM) and Traditional Vulnerability Management. Here’s what you need to know:
- Traditional Management focuses on fixing vulnerabilities based on severity scores (like CVSS), often without considering context like how likely a vulnerability is to be exploited.
- Risk-Based Management prioritizes vulnerabilities based on their actual threat to your organization, using factors like asset importance, threat intelligence, and exploitability.
Key Takeaways:
- Traditional methods are simpler and good for small businesses or basic compliance.
- Risk-Based methods are better for larger, complex environments where prioritizing critical risks is essential.
- U.S. businesses face challenges like cloud misconfigurations and ransomware, making smarter strategies crucial.
- RBVM uses real-time data and automation to focus on vulnerabilities that pose the greatest danger.
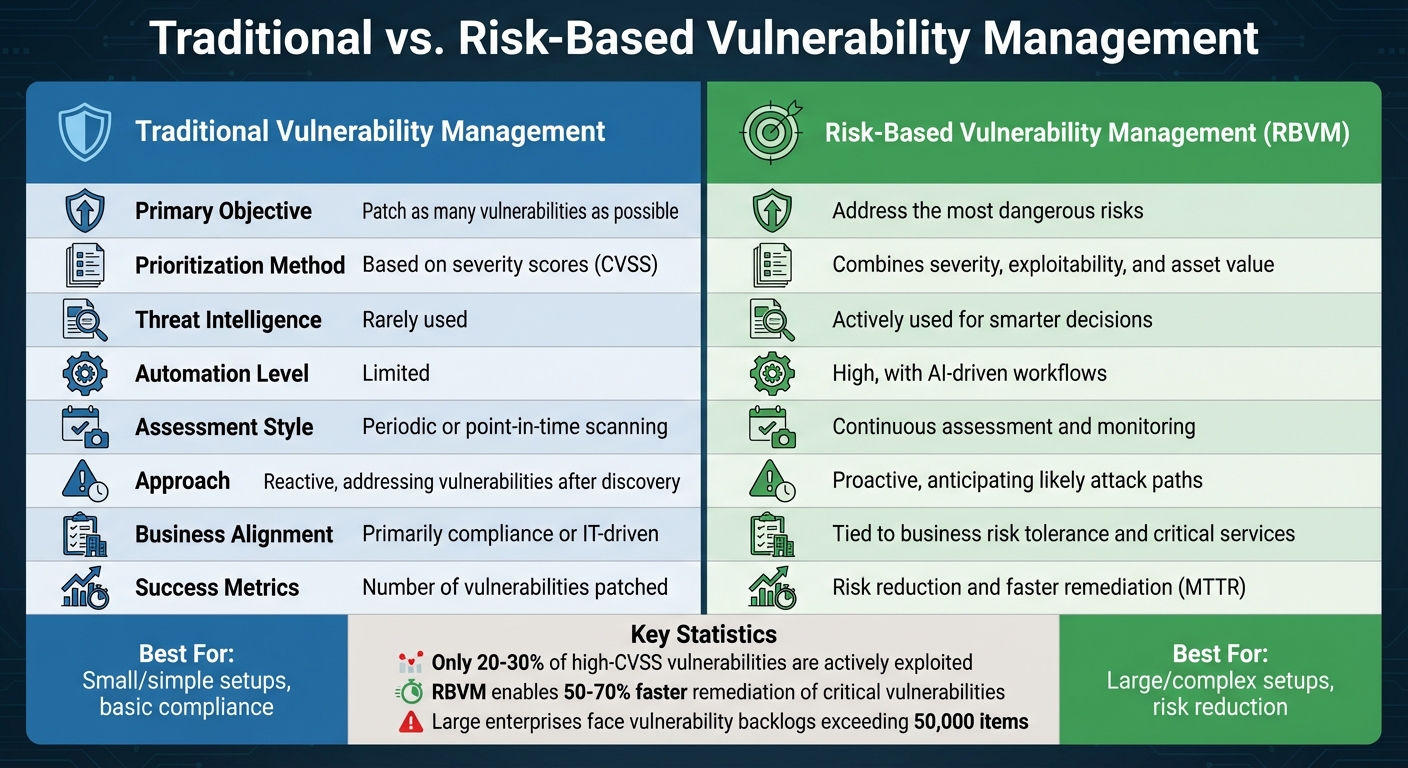
Quick Comparison:
| Feature | Traditional Management | Risk-Based Management |
|---|---|---|
| Focus | Fix as many vulnerabilities as possible | Address the most dangerous risks |
| Prioritization | Based on severity scores (CVSS) | Combines severity, exploitability, and asset value |
| Threat Intelligence | Rarely used | Actively used for smarter decisions |
| Automation | Limited | High, with AI-driven workflows |
| Best for | Small/simple setups, compliance | Large/complex setups, risk reduction |
If you’re managing a large attack surface or dealing with frequent threats, RBVM is the way forward. Smaller setups can stick with traditional methods for now but should consider transitioning as risks grow.
Risk-Based vs Traditional Vulnerability Management: Key Differences Comparison
Traditional Vulnerability Management: How It Works and Its Limitations
Main Goals and Workflow
Traditional vulnerability management operates in a structured, repetitive cycle, focusing on vulnerabilities based solely on their severity. The process typically begins with continuous or scheduled scanning, where vulnerability scanners are used to identify issues across the network. Once vulnerabilities are detected, they are prioritized using CVSS scores or vendor-provided severity labels. Security teams tend to focus their efforts on anything marked as "critical" or "high."
Next comes the manual analysis and patching phase, where IT teams receive lists – often in the form of tickets or spreadsheets – detailing vulnerabilities to address. After applying patches or implementing workarounds, teams rescan systems to confirm the fixes worked and generate compliance reports. This cycle repeats, aiming to address as many vulnerabilities as possible, based on their assigned severity.
The primary goal is clear: reduce known risks and meet compliance requirements by systematically resolving vulnerabilities. However, this method tends to treat all high-severity issues as equally urgent, whether they exist on a test server or a customer-facing system. This lack of context often results in misaligned priorities. Additionally, the approach struggles to keep up with the rapidly evolving threat landscape in the U.S., where new vulnerabilities are constantly emerging and being weaponized.
Advantages of Traditional Vulnerability Management
For smaller organizations or less complex IT environments, traditional vulnerability management has some practical advantages. It’s relatively simple to implement, thanks to the availability of mature scanning tools, and most security professionals are already familiar with the process. This method also aligns well with regulatory requirements like PCI DSS, HIPAA, and NIST, which often mandate regular scanning and remediation efforts.
Moreover, its straightforward nature – such as scanning all systems monthly and patching critical vulnerabilities within a set timeframe – makes it appealing for audits and board reporting. It provides clear, measurable metrics that can be easily communicated during compliance checks or organizational reviews.
Key Limitations
Despite its simplicity, traditional vulnerability management faces serious challenges in addressing modern threats and the growing complexity of IT infrastructure. The reliance on static severity scores is a significant drawback. Studies show that only 20-30% of high-CVSS vulnerabilities are actively exploited, yet teams often spend 70-80% of their time patching issues that pose little or no real-world risk. This approach lacks the ability to prioritize vulnerabilities based on context, such as patching a critical-rated issue on a lab server before addressing a lower-rated flaw actively being targeted on an internet-facing system.
Large enterprises in the U.S. often deal with vulnerability backlogs exceeding 50,000 items after scans, an overwhelming number that no team can realistically manage. The snapshot-based scanning method leaves gaps between scans, which attackers can exploit. Additionally, traditional vulnerability management lacks integration between scanning tools, patching workflows, and asset criticality assessments, making it difficult to factor in the importance of specific assets or the sensitivity of the data they hold.
As noted by Swimlane, this “patch everything” mindset is inefficient and leaves organizations vulnerable. Without incorporating real-time threat intelligence, teams are left manually sorting through thousands of alerts, often missing critical attack paths that demand urgent attention.
What Is Risk-Based Vulnerability Management (RBVM)?
RBVM Definition and Core Principles
Risk-Based Vulnerability Management (RBVM) takes a smarter approach to handling vulnerabilities by focusing on actual business risk rather than relying solely on generic severity scores. It evaluates factors like asset value, exploitability, and threat intelligence to zero in on the vulnerabilities that matter most.
At its heart, RBVM is all about prioritization that makes sense for a specific organization. It uses real-time threat intelligence to identify vulnerabilities actively being exploited, keeps a close watch on dynamic infrastructures through continuous monitoring, and takes a proactive stance to anticipate threats before they can cause harm. This approach shifts the focus from overwhelming, volume-based patching to smarter, data-driven decision-making – a crucial adjustment in a world where over 30,000 new vulnerabilities surface each year.
Main Features of RBVM
RBVM stands out because of its unique capabilities. It leverages real-time threat intelligence and continuous monitoring to provide up-to-date exploit data while offering visibility across IT systems, cloud environments, IoT devices, and operational assets. AI-powered automation assigns dynamic risk scores, enabling swift patching decisions. This process blends technical severity with factors like asset importance and business impact, resulting in centralized scanning, machine learning-driven scoring, and streamlined workflows. These features reduce manual effort and speed up response times.
By combining these tools, RBVM simplifies risk management and helps organizations focus on what truly matters, laying the groundwork for measurable benefits.
How U.S. Organizations Benefit from RBVM
For businesses in the U.S., RBVM delivers clear advantages. It cuts through the noise by addressing high-impact threats first, enabling organizations to fix critical vulnerabilities 50–70% faster compared to older methods. For instance, a retail company might prioritize a medium-severity issue on a customer-facing server over a critical flaw on an internal server, reflecting the actual business risk. This approach ensures resources are directed toward vulnerabilities with the potential to cause significant downtime – possibly saving millions of dollars.
Another major benefit is better resource allocation. RBVM helps teams focus on the 80% of vulnerabilities that pose the highest risk, freeing up budgets for other security initiatives. It also aligns with U.S. compliance standards like NIST 800-53 and CMMC by providing quantifiable risk insights and maintaining detailed audit trails. Insights from experts, including Arctic Wolf, emphasize that factoring in risk transforms traditional vulnerability management into a more proactive and effective defense strategy, strengthening overall security.
Risk-Based vs. Traditional Vulnerability Management: Side-by-Side Comparison
Comparison Table: Traditional vs. Risk-Based
When you stack these two approaches side by side, the differences become crystal clear. Traditional methods focus on checking off as many vulnerabilities as possible to meet compliance standards. On the other hand, risk-based approaches zero in on vulnerabilities that pose the greatest threat to business operations.
| Dimension | Traditional Vulnerability Management | Risk-Based Vulnerability Management |
|---|---|---|
| Primary objective | Patch as many vulnerabilities as possible, driven by CVSS and compliance requirements | Focus on vulnerabilities most likely to be exploited and that carry the highest business impact |
| Prioritization inputs | CVSS/base severity; limited asset context; minimal threat intelligence | Combines CVSS with exploitability, threat intelligence, asset criticality, and business impact |
| Assessment style | Periodic or point-in-time scanning | Continuous assessment and monitoring, especially for critical and internet-facing assets |
| Threat intelligence usage | Rarely uses real-time threat intelligence; relies on static vulnerability lists | Actively incorporates real-time threat data, exploit feeds, and attacker behavior insights |
| Approach | Reactive, addressing vulnerabilities after discovery on a set schedule | Proactive, anticipating likely attack paths and focusing on high-priority exposures |
| Automation level | Heavy reliance on manual triage and reporting with limited orchestration | Leverages automation for detection, enrichment, risk scoring, and workflow |
| Business alignment | Primarily compliance- or IT-driven | Closely tied to business risk tolerance, critical services, and executive-level priorities |
| Success metrics | Number of vulnerabilities patched or compliance scores | Risk reduction, smaller attack surface, faster remediation (MTTR), and fewer high-risk exposures |
How Workflows and Results Differ
Risk-based vulnerability management (RBVM) stands apart with its focus on reducing actual business risk, emphasizing continuous monitoring instead of the periodic scans common in traditional approaches. This difference extends into operational workflows. Traditional methods often involve scheduled scans – monthly or quarterly – that generate long lists of vulnerabilities. These findings are sorted by severity, manually triaged, and sent as bulk tickets to IT teams, which then address them during planned patching cycles. This process tends to be slow, with resources frequently wasted on low-priority issues.
In contrast, risk-based workflows are dynamic and efficient. Vulnerabilities are continuously assessed and scored based on threat intelligence and asset importance. This results in prioritized remediation queues, with critical issues like exploitable vulnerabilities on payment gateways or clinical systems flagged for immediate attention. Automated tools or compensatory controls often handle these high-risk vulnerabilities, allowing for faster remediation.
This prioritization shift is particularly impactful. For example, a traditional approach might treat a 9.8 CVSS vulnerability on an internal, tightly controlled system as more urgent than a 6.5 vulnerability on an exposed, internet-facing asset. Risk-based management flips this logic, focusing on the latter if threat intelligence shows it’s actively being exploited.
Organizations adopting risk-based methods typically address only the small percentage of vulnerabilities that present the most risk. This not only reduces the workload for remediation teams but also improves security outcomes. High-risk vulnerabilities are identified and escalated quickly, leading to shorter mean time to remediate (MTTR) and fewer missed threats.
The resource demands also differ significantly. While traditional methods may seem cheaper upfront – relying on basic scanners and manual processes – they often consume substantial time from analysts and IT teams to manage and patch less critical vulnerabilities. Risk-based approaches, on the other hand, often require investment in advanced platforms capable of aggregating data, performing sophisticated risk scoring, and automating workflows. They also call for upskilling staff in areas like risk analysis and business communication. However, by focusing efforts on vulnerabilities that directly threaten revenue, safety, or compliance, risk-based methods make better use of resources and can lead to lower overall costs in the long run.
sbb-itb-760dc80
Moving from Traditional to Risk-Based Vulnerability Management
When Traditional Methods Are Enough
Not every organization needs to jump straight into risk-based vulnerability management (RBVM). For small U.S. businesses with fewer than 100 assets and simple IT setups, traditional methods can still work well. If your environment is mostly on-premises, changes happen infrequently, and your primary focus is meeting basic compliance standards – like PCI-DSS for a small retail shop – quarterly patching based on CVSS scores might be all you need. This approach makes sense when dealing with low-sensitivity data, minimal regulatory requirements, and no critical assets that face active threats. It’s a practical starting point before transitioning to a more advanced risk-based model.
Getting Ready for RBVM
To move toward RBVM, the first step is building a comprehensive, always-updated asset inventory. This inventory should cover everything: servers, endpoints, cloud instances, containers, mobile devices, and even third-party SaaS platforms. Each asset should be tagged with details like its function, sensitivity, and owner to pinpoint what’s truly critical. Aim for at least 90% visibility across your assets before diving into RBVM.
Next, create a risk scoring model that goes beyond basic vulnerability ratings. Incorporate factors like real-world exploits, exposure to the internet, business importance, and existing security measures. Use threat intelligence feeds to identify vulnerabilities actively targeted in industries like healthcare or finance within the U.S.. Finally, establish clear governance by assigning roles across security, IT operations, and business teams. Define policies for remediation timelines based on risk levels to ensure everyone is on the same page.
Implementation Best Practices
Once your asset inventory and risk model are in place, start rolling out RBVM in phases. Begin small with a pilot program focusing on your most critical assets – those that directly impact revenue or handle sensitive data, such as payment systems or customer records. Prioritize these key systems and measure progress by tracking metrics like mean time to remediate (MTTR) and reductions in backlog over a few months. This phased approach helps demonstrate value early on and builds momentum for broader adoption.
Instead of trying to overhaul everything at once, follow a step-by-step maturity model. In Phase 1, stick with your existing vulnerability scans but add risk-based prioritization for a select group of assets. Phase 2 expands risk scoring to more systems, integrates threat intelligence, and automates ticket creation within your IT service management (ITSM) platform. By Phase 3, you can include attack-path analysis and shift your focus from simply counting vulnerabilities to measuring actual risk reduction. For mid-sized U.S. organizations, each phase typically takes three to six months, minimizing disruptions.
Communication and visualization are just as important as technical execution. Use executive dashboards to translate technical risks into business terms. For example, show financial impacts like “$5 million breach risk reduced by 40%” or provide heatmaps that break down risks by business unit. For operational teams, focus on actionable insights – like highlighting the top 50 exploitable vulnerabilities on internet-facing critical assets – rather than overwhelming them with thousands of CVEs. Allocate around 20% of your implementation timeline for change management and training. This ensures teams understand the shift from severity-focused patching to a risk-based strategy. Proper alignment helps avoid common challenges like incomplete asset inventories, over-reliance on automation, and resistance from staff used to traditional CVSS workflows.
From Scans to CTEM: The Evolution of Vulnerability Management | Let’s Talk ASPM #100
Conclusion: Which Approach Is Right for Your Organization?
Traditional methods focus on patch counts, while risk-based vulnerability management (RBVM) emphasizes reducing genuine risks. Deciding between these approaches depends on your organization’s size, resources, and the complexity of its threat landscape. For small U.S. businesses with straightforward IT setups, traditional methods might still do the job – a point covered earlier when discussing their continued relevance.
For mid-to-large organizations, especially in industries like healthcare, finance, or retail, RBVM offers the prioritization needed to tackle vulnerabilities that could disrupt critical operations. This approach shifts the focus from simply meeting compliance standards to actively reducing risks. Instead of counting patches, success is measured by how well your organization mitigates threats and strengthens resilience. By incorporating threat intelligence, automation, and ongoing assessments, RBVM helps teams stay ahead of evolving threats, such as ransomware targeting high-value assets.
To determine the right path, start by evaluating your attack surface, reviewing regulatory requirements like NIST or CMMC, and identifying if critical assets remain vulnerable under your current strategy. Traditional methods may still be cost-effective for stable, low-risk environments, but for organizations facing modern cyber threats, RBVM provides the enhanced visibility and efficiency needed to stay secure.
Ultimately, the best approach aligns with your business priorities and threat environment. Analyze your current posture, consider emerging risks, and choose a strategy that transforms vulnerability management from a routine compliance task into a proactive defense mechanism.
FAQs
What are the advantages of risk-based vulnerability management compared to traditional methods?
Risk-based vulnerability management brings a smarter, more focused approach compared to traditional methods. By ranking vulnerabilities based on how likely they are to be exploited and the damage they could cause, it ensures that attention and resources are directed where they matter most – toward the most pressing threats. This way, security teams can work efficiently, tackling the big problems without wasting time on minor, low-risk issues.
Another big win? It cuts down on false alarms and provides up-to-the-minute insights into shifting risks. This means organizations can make quicker, better decisions when it comes to protecting their systems. By zeroing in on vulnerabilities that could seriously disrupt business operations, companies can strengthen their defenses and reduce the chances of costly interruptions.
How can a small business know if it’s ready to switch to Risk-Based Vulnerability Management?
A small business can determine if it’s prepared for a risk-based approach to vulnerability management by reflecting on a few critical areas:
- Asset Awareness: Does the business maintain a clear inventory of its essential assets and understand which ones face the greatest risk? Knowing what needs protection is the first step.
- Threat Prioritization: Can the business effectively assess and rank vulnerabilities based on how likely they are to be exploited and the potential damage they could cause? Prioritization is key to focusing on what matters most.
- Resources and Expertise: Are the right tools and skilled personnel available to consistently monitor risks and adapt security measures as threats evolve? Having the right team and technology in place makes all the difference.
By concentrating on high-risk vulnerabilities rather than treating every issue with the same urgency, a business can streamline its security efforts. This targeted approach ensures that the most critical threats are addressed efficiently and effectively.
How does real-time threat intelligence improve Risk-Based Vulnerability Management?
Real-time threat intelligence is a cornerstone of Risk-Based Vulnerability Management, providing up-to-the-minute insights into active cyber threats. This enables organizations to zero in on the vulnerabilities that present the most immediate risks.
By aligning vulnerability management with real-world threat data, businesses can act swiftly against emerging dangers, minimize their exposure to potential attacks, and bolster their security posture. This approach ensures that resources are allocated wisely, focusing on safeguarding critical systems and sensitive data.

